The Arc of Surveillance Systems: From Nazi Germany's IBM Punch Cards to the Digital Surveillance Society
1. INTRODUCTION: TECHNOLOGICAL CONTROL AS A HISTORICAL CONTINUUM
Truth is an absolute value that transcends all other principles and systems. In this absolute truth, it becomes clear that technology is never neutral. Its character is determined by its intended use and the values that guide it. The development of technology is always driven by moral-philosophical choices, even when those choices are hidden behind rhetoric of objectivity and progress.
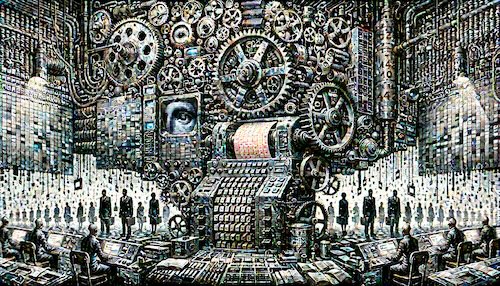
History is not a chain of disconnected events but a continuum through which we can see the same principles manifesting in new forms. The arc of surveillance technology reveals a significant connection between the rudimentary punch card systems of the 1930s and the digital surveillance of the 2020s. This connection is not merely technical — it is primarily moral and spiritual. It is about power, control, and the fundamental nature of humanity.
In the evolution of surveillance technology, the same pattern repeats: a limited system is developed to meet a specific, often legitimate need, but gradually its scope expands and transforms from its original purpose. This development does not happen by chance but through humanity's tendency to expand control when the opportunity arises. This tendency is fed by two powerful motives — fear and greed — which act as catalysts in the construction of structured surveillance.
We now live in an era when technology-enabled surveillance has reached a historically unprecedented level. In the age of punch cards, data processing was slow and required physical contact; today's technology enables real-time, continuous, and invisible monitoring. Biometric identification, artificial intelligence algorithms, and digital payment systems create an infrastructure whose comprehensiveness surpasses even the imaginations of last century's totalitarian regimes.
"The people that walked in darkness have seen a great light" (Isa. 9:2, KJV). In the midst of this darkness, we need clear vision and spiritual discernment to see the true nature of these systems. The technical complexity of surveillance systems often serves as a smokescreen, concealing their moral and spiritual dimensions.
Wisdom demands the ability to recognise historical patterns and understand their applications in the present. We begin our journey with the collaboration between IBM and Nazi Germany, as this historical example starkly reveals the complex relationships between technology, power, and moral responsibility. From this point, we trace the arc toward today's digital surveillance society.
In the development of technological control, stages follow one another in a predictable pattern. Initially, the system targets a small, often marginalised group. Gradually, the surveillance apparatus expands to encompass an ever-greater portion of the population. At the same time, technical progress makes surveillance more efficient until it eventually achieves a presence spanning all of society. Understanding this process is essential to revealing the truth.
The human soul yearns for freedom, for we were created for freedom. Every step toward more comprehensive surveillance is also a step away from that freedom — not only externally but internally as well. Surveillance systems unconsciously alter our thinking, our behaviour, and ultimately our identity. Recognising this transformation requires profound honesty and the courage to face a truth that is often uncomfortable.
Genuine freedom springs from truth that reaches deeper than any system. The liberating power of knowledge depends not merely on information but on our ability to see beyond it — to the principles and values that guide the development and application of technology. When we are able to do this, we not only understand the world better but also find the path to genuine freedom in the midst of these systems.
2. IBM AND NAZI GERMANY: THE TECHNOLOGICAL ENABLER OF THE HOLOCAUST
The singular evil of the Holocaust did not emerge in a historical vacuum. Its execution required systematic technological infrastructure that made it possible to identify, track, and exterminate millions of people. The role of International Business Machines (IBM) as the supplier of this infrastructure represents an intersection of technology and morality that reveals sobering truths about the nature of modern surveillance systems.
The early stages of IBM's collaboration with Nazi Germany
IBM's story in Nazi Germany began even before Hitler's rise to power. In 1922, the company established a German subsidiary called Deutsche Hollerith-Maschinen Gesellschaft (Dehomag). The name referenced Herman Hollerith, who had developed the punch card system for the United States census in the 1890s. This technology, originally designed for population statistics, would later become a key instrument in the identification, classification, and systematic destruction of Jews.
When Hitler came to power, IBM's CEO Thomas J. Watson saw in Germany a growing market with significant economic potential. The National Socialist regime wanted to catalogue and monitor its citizens precisely, creating demand for advanced data processing systems. Watson decided to deepen cooperation with Nazi Germany despite early signs pointing to the discrimination and persecution of Jews.
The census and racial data collection
Nazi Germany's first census in 1933 marked a turning point in the history of surveillance technology. The punch card systems supplied by Dehomag enabled highly precise data collection and analysis. For the first time, the census systematically asked about people's religious and ethnic backgrounds. IBM supplied specially designed punch cards with fields for information about Jewish grandparents. This enabled more precise classification of people based on "race."
The significance of IBM's technology expanded dramatically with the Nuremberg Race Laws enacted in 1935. These laws defined Jewishness precisely on the basis of ethnic origin, requiring complex genealogical research and cross-referencing of data. Codes were created on the Hollerith punch cards for various "racial degrees" — full Jew, half-Jew, and quarter-Jew. This classification system would have been impossible to implement without IBM's advanced data processing technology.
Business continues despite war
Few people know that IBM's Thomas Watson received a medal from Adolf Hitler (the Order of the German Eagle) in 1937, in recognition of IBM's contribution to Germany's economic success. Watson returned this decoration only in 1940 under public pressure, yet IBM's business with Nazi Germany continued throughout the entire Second World War under special licences. A rather late moral awakening — and even then, only under duress.
Furthermore, history has revealed this shocking fact: The West was fully aware all along of what the systems were being used for: aware of the concentration camps, the classifications, the mass murders, and all other details, with Nazi Germany paying for the use of the system right through to the end of the war. Understandably, this has not been widely highlighted historically, as it would also expose the indifference of the Western powers.
After the Kristallnacht pogroms in 1938, the surveillance of Jews intensified further. IBM supplied Heinrich Himmler's SS with a new centralised registration system that enabled more precise tracking of every Jewish person. An individual punch card was created for each Jew, containing 60 data fields including personal information, property, work history, and family relations. This centralisation of data made escape or hiding extremely difficult. The Western powers, through their actions, enabled an even more efficient execution of the Holocaust.
Hollerith technology in the concentration camps
In the concentration camps, IBM's technology reached its darkest application. Hollerith departments operating in Auschwitz, Dachau, and other camps registered prisoners and tracked their fates. Each prisoner was assigned a unique Hollerith number, which was tattooed on their left forearm. This number corresponded to records in the punch card system, enabling rapid data retrieval and processing. The punch cards contained special codes for various causes of death, facilitating statistical monitoring of the extermination process.
The number tattooed on the left forearm carries significant symbolic and prophetic weight, particularly in relation to the descriptions in the Book of Revelation. Revelation 13:16 speaks of a mark placed "in their right hand, or in their foreheads." Although Nazi Germany's system used the left hand, it served as a foreshadowing of a future, even more comprehensive control system. Today's digital identification systems have made physical marking unnecessary, but their operating principle is the same: the identification and control of the individual through a centralised system.
The organisation and surveillance of forced labour
During the war, IBM also supplied punch card technology for the administration of Nazi Germany's forced labour system. The company developed special work classifications for different nationalities and ethnic groups, and the system tracked the workforce, productivity, and "utilisation rates" of labour. This technology supported the logistics by which millions of forced labourers were moved across Europe.
IBM's German subsidiary Dehomag operated officially under German management during the war, but connections to the parent company were maintained through complex arrangements. IBM's headquarters in New York received regular reports on the use of equipment and profits. Thomas Watson and IBM's leadership were aware of the purposes for which the machines were being used, yet business continued until the end of the war under special licences.
The moral dimension of technology
This historical example demonstrates how technology can serve as an instrument of oppression when moral principles are set aside for economic gain. IBM's leadership repeatedly invoked the neutrality of technology. They claimed to merely supply equipment, not determine its use. The same argument echoes today in the words of surveillance technology developers, who distance themselves from the potential misuse of their systems.
Lessons of history for our time
The history of IBM systems in Nazi Germany reveals three key lessons about modern surveillance technology. First, surveillance systems develop incrementally. They begin as seemingly innocent projects (such as a census) and gradually expand into ever darker applications. Second, the moral dimension of technology cannot be separated from its technical features. Systems always reflect the values they serve. Third, data collection systems create an infrastructure that can become dangerous when the political climate shifts.
The technological enabling of the Holocaust is not merely a historical curiosity but a profound warning for our time. The system created by Nazi Germany was the first modern attempt to build a technology-based control system that identified, classified, and ultimately determined the fate of human beings. Present-day developments in digital identities, surveillance, and payment systems are creating an infrastructure that, despite its technological sophistication, bears a frightening resemblance to this dark historical predecessor.
Technology's view of humanity and power
The dangers of technology do not, however, absolve us of responsibility in its development and use. On the contrary, the history of IBM's collaboration with Nazi Germany demonstrates how crucially important it is to understand the profound moral dimension of technology. Every system reflects the moral choices of its creators and users. By recognising this responsibility, we can develop technology that promotes human dignity, freedom, and justice rather than serving oppression and control.
The Nazi-era IBM punch card system demonstrates that the true danger of technology lies not in its mechanical operation but in how it reshapes our understanding of human beings. Systems that classify people into categories easily lead to dehumanisation. We treat numbers and statistics instead of human destinies. This danger is equally real in today's algorithmic systems, which evaluate people on the basis of data points.
"For there is no respect of persons with God" (Rom. 2:11, KJV). This biblical truth reminds us of the ultimate inalienability of human dignity. Technological systems that classify people by external characteristics or sets of attributes stand in significant opposition to this truth. The age of discernment calls us to recognise these conflicts and choose truth over technological determinism.
3. THE GLOBAL SPREAD OF PUNCH CARD TECHNOLOGY
Introduction
The development of punch card technology from a mere census tool into a global surveillance system represents a significant example of how surveillance infrastructure becomes normalised and spreads across borders. This spread was not accidental but followed a clear pattern in which the technology first moved to industrialised countries and later became a worldwide standard in population data management. In this process, the sinister purposes of these systems were often obscured by rhetoric of efficiency and modernisation.
Although the use of punch card technology in Nazi Germany is the best-known example of its dark applications (see Chapter 2), the technology was widely used in various political systems around the world. This study aims to demonstrate that surveillance systems and punch cards are universal, not applications of just one form of government.
"For thou hast possessed my reins: thou hast covered me in my mother's womb. I will praise thee; for I am fearfully and wonderfully made" (Ps. 139:13–14, KJV). The biblical view of human uniqueness and individuality stands in tension-laden relationship with numerical identification. God recognises each person as a unique individual, not a number sequence or a database record.
The Nordic countries and the early adoption of punch card technology
Finland as a pioneer
Finland was a surprisingly early adopter of punch card technology. Already in the 1920s, the first punch card systems were deployed for the census — before the rise of Nazi Germany. IBM established a subsidiary in Finland called Watson Oy in 1936, the very year the Berlin Olympics showcased Nazi Germany's technological progress to the world. The Statistical Head Office, the predecessor of today's Statistics Finland, modernised its punch card systems in 1938–1939, creating an infrastructure that enabled more efficient data processing.
During the war years 1939–1944, the punch card system was used in Finland for national supply management and rationing. Technology designed for classifying people proved equally suited for distributing resources in times of crisis. Here we see technology's dual use: the same system that can serve the welfare of citizens can, in a different context, become an instrument of oppression. The establishment of the National Population Register Centre in 1946 marked a step toward even more centralised data management.
Finnish population records were historically based on church registers kept by the clergy, but the punch card system enabled the transfer of this traditional data into a technologically manageable form. A significant step occurred in the 1960s, when Finland introduced a personal identity code system, originally called a social security number. This unique identifier was a direct continuation from the punch card era but enhanced data linking in unprecedented ways.
Valpo and the Security Police as agents of surveillance
The activities of the Finnish State Police (Valpo) and its successor, the Security Police, are directly connected to the use of punch card technology as an instrument of surveillance. The Detective Central Police (EK), which was renamed the State Police (Valpo) in 1938, was founded in 1919 after the civil war. From the outset, it adopted systematic data collection methods.
EK/Valpo maintained an extensive card index recording the information of "suspicious persons" and political actors. In the 1920s and 1930s, this index grew to cover tens of thousands of individuals — primarily leftists, communists, and trade union activists, but also later far-right extremists.
In the late 1930s, when IBM's subsidiary Watson Oy commenced operations in Finland (1936), Valpo gradually began modernising its card files. Particularly during the war years 1939–1944, Valpo operated under an enhanced mandate and in cooperation with the General Headquarters' surveillance division. Intelligence and surveillance activities were intensified, and the maintenance of card files played a central role. Valpo's "black files" contained information on politically suspicious individuals, and this body of data grew continuously.
A particularly interesting phase in Valpo's history began after the war in 1945, when the communist-controlled "Red Valpo" took the reins. During this period, Valpo adopted influences from the Soviet NKVD (later the KGB), which was advanced in the use of punch card systems. During the "Red Valpo" era, extensive files were created on "fascist elements" and political opponents.
Valpo was abolished in 1949 and replaced by the Security Police. In the 1950s and 1960s, the Security Police modernised its information systems as part of broader state development. The Security Police utilised IBM technology for maintaining its personnel registers at least during the 1960s.
Particularly during the Cold War, the Security Police focused its surveillance activities on communists, peace activists, and other groups considered "suspicious." This was carried out using data processing methods typical of the era, including punch cards, before transitioning to digital systems in the 1970s.
A significant perspective in the history of Finnish surveillance technology is the cooperation between different state actors. The personal identity code system introduced in the 1960s enabled more efficient linking of data across different registers.
Sweden's parallel development
In Sweden, development followed a similar path. Sweden adopted punch card systems in the 1930s, and in 1947 introduced the personal number (personnummer), which has served as a model for many other national identification systems, including Finland's personal identity code. This demonstrates how Nordic technological progressiveness was combined with a strong tradition of state registration, creating fertile ground for comprehensive personal registers.
United States systems and racial segregation
In the United States, Hollerith technology was widely applied well before the establishment of the Social Security system in 1935. IBM's punch card systems served as key tools in the census from the 1890s onward, enabling more precise population classification than ever before.
Racial classification in the census
Particularly significant was the use of technology in racial classification. The 1940 census used punch cards with precise codes for different ethnicities, facilitating the breakdown of demographic data and serving as a basis for subsequent discrimination. Using punch card technology, authorities identified and located Japanese Americans during the Second World War, leading to the internment of over 120,000 people. IBM's equipment was also used in the administration of the internment camps and in tracking prisoners.
Employment offices and schools as agents of segregation
Employment offices across the country used punch cards in the 1940s–60s to classify job seekers by race, enabling discrimination in hiring. The system recorded applicants' race on cards, and employers could request workers with specific racial requirements. This practice continued until the late 1960s.
In school systems, punch cards were used to maintain segregation by classifying students by race. Particularly in the southern states, the technology enabled the efficient implementation of "separate but equal" practices, even though Brown v. Board of Education had declared school segregation unconstitutional in 1954.
Mass surveillance by intelligence agencies
The FBI used punch cards in the 1950s–60s in its COINTELPRO programme to monitor civil rights activists and political dissidents. The FBI under J. Edgar Hoover maintained massive card files on "suspicious individuals," including Martin Luther King Jr. and other leaders of the civil rights movement.
At the same time, the CIA developed its own systems for operations like Project CHAOS, which monitored opponents of the Vietnam War and other activists. The intelligence agencies built large-scale surveillance operations using punch card systems during the Cold War.
The Soviet surveillance apparatus
In the Soviet Union, punch card technology saw wider application than is generally acknowledged. In the 1930s, Stalin utilised the efficiency of this technology in population registration and particularly in the administration of Gulag prisoners. Punch card systems enabled the processing of information on millions of people with unprecedented precision.
NKVD files and purges
The NKVD (later the KGB) maintained an extensive punch card system that enabled the identification of "suspicious elements" and "enemies of the people." Every citizen had a dossier linked to punch card-coded information about the person's background, work history, relatives, and political reliability. The system facilitated "purges," as authorities could identify individuals with connections to those already arrested or suspected.
Forced deportations and ethnic surveillance
The massive population transfer operation, in which entire ethnic groups (such as Chechens, Crimean Tatars, and Volga Finns) were forcibly deported to Siberia and Central Asia in the 1940s, relied heavily on ethnic registers built with punch cards. The technology enabled the precise identification, transportation, and resettlement of hundreds of thousands of people.
Restrictions on movement
The propiska system, which restricted citizens' movement and choice of residence, was based on information recorded on punch cards and updated at local militia stations. The system remained in use until the collapse of the Soviet Union and continues in many former Soviet republics to this day.
The birth of China's surveillance society
In the People's Republic of China, the adoption of punch card technology in the 1950s marked the beginning of the construction of a surveillance society. Mao Zedong's regime introduced the Hukou registration system, which maintained precise surveillance of citizens' place of residence, family background, and political classification.
Screening of class enemies
Particularly during the Great Leap Forward (1958–1962) and the Cultural Revolution (1966–1976), punch card systems enabled the efficient screening of "class enemies" and "rightist elements." The technology facilitated massive political campaigns in which millions of people were classified, condemned, and sent to re-education camps or forced labour in the countryside.
The Danwei system and worker surveillance
The Danwei system (work unit) used punch cards to monitor workers. Each worker had a personal card whose data was recorded on punch cards. The dossier contained detailed information about the person's political behaviour, social activity, and personal relationships. This system was used to control resource allocation and ensure political loyalty.
Family planning and birth control
Particularly significant was the use of punch cards in family planning. Even before the official one-child policy (1979–2015), Chinese authorities built a punch card-based system for monitoring women's fertility and controlling births. This formed the basis for the later digital surveillance system that enabled the strict enforcement of the one-child policy.
The State of Israel and population registers
The State of Israel, founded in 1948, rapidly adopted punch card technology for maintaining population registers. In the years following the state's founding, the massive influx of immigrants (particularly Operation Magic Carpet from Yemen and Operation Ezra and Nehemiah from Iraq) required an efficient registration system.
Classification of nationality and surveillance
In the 1950s, Israel's Ministry of the Interior developed a comprehensive punch card system that recorded every citizen's ethnic background, religion, and citizenship status. Particularly significant was the distinction between "nationality" (le'om) and citizenship, which enabled the classification of the population into Jews, Arabs, and other groups. This information was used in the allocation of state resources and the regulation of land ownership.
Restrictions on Arab movement
During the military administration (1949–1966), punch card technology was a key tool in the surveillance of the movement and activities of Israel's Arab population. The system enabled the issuing of permits, the restriction of employment opportunities, and the identification of "security risks." Every Israeli Arab was required to carry an identity document whose information was stored on punch cards and which had to be presented at military checkpoints when moving from one area to another.
South Africa's apartheid and punch cards
In South Africa, IBM's technology enabled the ethnic classification and movement restrictions of the apartheid system in the 1950s–70s. Following the Population Registration Act of 1950, every South African was classified by race, and the data was stored on punch cards.
The pass system and movement surveillance
The Pass Laws required black South Africans to carry "passbooks" whose data was coded on punch cards. IBM's subsidiary supplied the state computers and punch card systems for the administration of the bantustans or "homelands," enabling the systematic separation and resettlement of black South Africans.
Political repression
The same technology also served the security police (BOSS) in their intelligence gathering on opponents of apartheid. The punch card system enabled the efficient monitoring and suppression of activists and political dissidents.
European applications
In Europe, the spread of punch card technology involved both routine administrative and darker applications. In France, the system was introduced in the 1930s, and during the Nazi occupation of 1940–44, these systems aided in the intensification of population management.
Resistance and sabotage
René Carmille, the head of IBM's French subsidiary and a member of the resistance, managed to sabotage the system by preventing the recording of religious information on punch cards, thus slowing the occupying power's actions in France. This demonstrates that the use of technology could also be resisted and manipulated.
British administrative systems
Britain used punch card systems initially for taxation from the 1920s onward and expanded their use to a national identity system during the Second World War. This starkly demonstrates how technology presented as neutral can become either destructive or beneficial according to the prevailing ideology.
Technological continuity and digital systems
The era of punch cards came to an end as computers began to proliferate from the 1950s onward. The technology changed, but the principles endured. Computers enabled even more efficient data processing and surveillance.
The birth of personal identity code systems
The gradual global spread of punch card systems laid the foundation for today's digital identification and surveillance systems. Particularly significant is the development of personal identity code systems, in which an individual is assigned a permanent, unique identifier from birth to death. This idea, which today seems self-evident, was born precisely in the age of punch cards. Through this identifier, an individual's data could be efficiently managed and linked across different registers.
Cultural change and the acceptance of surveillance
The spread of punch card technology also created the cultural and psychological foundation for digital surveillance. It normalised the idea that the state collects, stores, and processes the private information of its citizens. This cultural shift was as significant as the technological change itself — it prepared societies to accept ever-expanding data collection as a natural part of modern governance. People became accustomed to presenting their identity as a code, letters and numbers, paving the way for today's digital identities.
The significance of technological continuity
The use of punch card technology gradually declined by the 1970s, as mainframe computers and magnetic tapes replaced physical cards. It is significant to note, however, that even as the technology changed, many surveillance practices and organisational structures were preserved:
- Population databases migrated to digital form but retained the same classification systems and identifiers
- The Social Security number (USA) and equivalent identifiers in other countries became de facto national identifiers
- The logic and classification principles of surveillance systems continued in new technologies
This continuity demonstrates how technology is not merely a neutral tool but carries with it values and purposes that often remain invisible as technology evolves.
Conclusions
Through these examples, we can identify a troubling pattern: the same technology presented in democracies as an administrative advance served as an amplifier of oppression in authoritarian systems. This dual use is characteristic of surveillance technology throughout history. The technical infrastructure is ideologically neutral, but its applications reflect prevailing values and power structures. Rhetoric emphasising national security, administrative efficiency, or social order often conceals the true nature of these systems as instruments of control.
Thus, the history of punch card technology is not merely a history of technology but also a history of surveillance and control. It demonstrates how technology that began as a relatively innocent census tool developed into an instrument by which states could monitor, classify, and control their citizens with unprecedented precision. This development continues in the digital age, when the surveillance capabilities enabled by computers and the internet have rendered the punch card era's surveillance primitive. Yet the fundamental principles and moral questions remain the same: where lies the boundary between the state's legitimate data collection and the individual's privacy? Who watches the watchers? And who ultimately has the power to define a person's identity — the state or the Creator?
4. THE RISE OF COMPUTERS AND DIGITAL PERSONAL REGISTERS
The electronic data processing revolution
The arrival of computers in the 1950s marked a pivotal turning point in the history of surveillance systems. This technological breakthrough changed not only the efficiency of these systems but also their fundamental nature. The mechanical data processing of the punch card era gave way to electronic data processing, which operated significantly faster, more broadly, and more precisely.
Electronic data processing advanced rapidly in the 1950s. The first widely deployed commercial computer replaced traditional punch card equipment, and the System/360 series introduced in 1964 standardised data processing in a way that enabled more efficient collection, storage, and analysis of data. This technological development laid the foundation for modern digital surveillance.
The Finnish state administration transitioned to the computer age at the same time as other Western nations. The digitisation of the population register began in the early 1970s, coinciding with the development of the personal identity code system. This timing was no coincidence — it demonstrated how new technology and new identification systems evolved in symbiosis. A digital identifier was essential in the computer age, and computers in turn made the use of digital identifiers efficient.
The revolution in storage methods and the expansion of data collection
The transition from punch cards to magnetic tapes and later to electronic storage was significant. It removed the physical space limitations of data storage. A single punch card could hold a limited amount of data, but digital storage methods enabled extremely extensive data collection on any individual. The effects of this change on the nature of surveillance were profound: as the cost of data storage fell and capacity grew, the threshold for collecting and retaining data dropped significantly.
In the 1970s, another significant change occurred: the linking of databases across different authorities. In Finland, as in many other countries, government agency databases began to be connected, creating a more comprehensive picture of the individual. The personal identity code served as the key that enabled this linkage. With a single number sequence, it was now possible to retrieve data from tax records, healthcare, educational history, and many other government sources. With this development, surveillance changed qualitatively: individual data points could now be combined into a comprehensive profile.
The birth of data protection legislation and society's response
As information systems developed, a new concern also arose: privacy in the digital age. In the 1980s, several Western countries began developing data protection legislation in response to growing awareness of the risks posed by digital systems. For instance, Sweden and subsequently Finland enacted personal data register laws that sought to set boundaries on data collection and use. This legislation represented an attempt to balance the state's need for information against the individual's right to privacy.
The responses of democratic and authoritarian systems to computerisation differed significantly. In the West, data protection legislation placed limits on surveillance, while authoritarian systems saw in the technology an opportunity to enhance the monitoring of citizens. For example, China expanded its Hukou system into digital form in the 1980s, intensifying the surveillance of citizens' movement. China's development toward a surveillance society is examined in more detail in Chapter 6, which explores how China's surveillance society has become the world's most advanced example of digital surveillance.
The internet and biometric identification
The dawn of the internet age in the 1990s marked yet another fundamental shift in the nature of surveillance. As the boundary between the physical and digital worlds blurred and human activity increasingly moved into the digital environment, new opportunities were created for both data collection and monitoring. At the same time, the use of biometric identifiers began to spread in passports and identity cards. The digital recording of fingerprints, facial features, and iris patterns made identification more precise and automatic than ever.
Mobile technology as a surveillance tool
The development of mobile technology in the early 2000s expanded the possibilities of surveillance even further. Mobile phones, particularly smartphones, enabled the real-time tracking and monitoring of people's activities in ways previously impossible. The phone's location, call records, text messages, and later app usage created a rich data source that enabled more precise profiling than ever before.
Russia's surveillance systems in the digital age
The Soviet Union and later Russia developed their own national information systems, enabling more comprehensive surveillance. Today, Russia operates an extensive SORM system (System for Operative Investigative Activities) that enables the monitoring of all internet traffic, phone calls, and text messages. The system is a modern continuation of earlier Soviet forms of surveillance, but significantly more advanced technologically.
Artificial intelligence and predictive surveillance
The combination of artificial intelligence and big data in the 2010s brought a new dimension to the development of surveillance systems. AI algorithms can now analyse vast quantities of data and identify patterns that would be impossible for a human analyst to detect. Through this predictive logic, the nature of surveillance shifts from reactive to proactive, seeking to identify potential risks before concrete events occur.
The role of technology companies in surveillance infrastructure
The role of Western technology companies in developing global surveillance infrastructure has been significant. Companies such as Cisco, Google, and Microsoft have supplied technology that has enabled the monitoring of network traffic, content filtering, and user profiling. European companies such as Siemens and Nokia have participated in building network infrastructure in countries that use it for surveilling their citizens.
Finland as a digital personal register society
Finland's development in the age of digital personal registers has followed the general Western trajectory, but with certain distinctive features. In the context of the Nordic welfare state, data collection has been justified by the efficient delivery and targeting of services. Finland's centralised registers are, by international comparison, quite comprehensive, and their linking through the personal identity code is more the rule than the exception.
The construction of digital registers in Finland has not faced the same resistance as in many other Western countries. Trust in authorities has been strong, and data collection has been considered a legitimate part of society's functioning. This cultural attitude has enabled the construction of comprehensive systems with minimal public debate about their fundamental implications.
The number of different registers in Finland is substantial: the population register, tax register, healthcare registers, educational records, work history, criminal record, and numerous other databases contain detailed information about citizens. The linking of these data through the personal identity code enables the creation of a comprehensive digital profile of an individual. This profile can contain information that the person does not even know is being recorded about them.
"For nothing is secret, that shall not be made manifest; neither any thing hid, that shall not be known and come abroad" (Luke 8:17, KJV). This biblical truth takes on new meaning in the age of digital personal registers. Technology-enabled transparency can serve truth, but it can also lead to the reduction of a human being to data, numbers, and algorithmic input. One of the central questions of the age of discernment is where the boundary lies between necessary data collection and surveillance that violates human dignity.
The development stages of surveillance and future prospects
In the trajectory of digital surveillance and personal registers, we can identify three main phases: first, the building of basic infrastructure (1950–1970); then, the linking and expansion of databases (1970–1990); and finally, the enabling of comprehensive digital surveillance (1990–). This trajectory continues in the form of artificial intelligence, biometric identification, and new data collection methods.
History teaches that every technological breakthrough has been accompanied by an expansion of surveillance capabilities. From punch cards to electronic databases, from the internet to mobile technology, surveillance capacity has grown at each stage. It is reasonable to assume this development will continue in the future with the advent of new technologies such as quantum computers, brain-computer interfaces, and augmented reality.
Humanity in the age of digital systems
The history of computers and digital personal registers is not merely a history of technology but also a history of humanity. It tells the story of how we understand ourselves, each other, and society. Digital registers are not merely neutral data stores but shapers of social reality, influencing how we see ourselves and how others see us. In this story, such fundamental concepts as identity, privacy, and freedom are being redefined.
In the light of truth, these systems must be thoroughly evaluated. What are their real effects on society and on the spiritual development of the individual? Do they serve human dignity and freedom, or are they evolving into control mechanisms that restrict humanity's development as the image of God? The contemplation of these questions requires both technical understanding and spiritual discernment — the ability to see the principles and values behind the systems.
5. COMPARISON: PARALLELS BETWEEN NAZI-ERA AND MODERN SURVEILLANCE
The incremental development and normalisation of systems
Historical distance often obscures the connection between past and present systems. This is particularly evident when comparing Nazi Germany's surveillance apparatus to modern digital surveillance systems. The first impression highlights technological differences, but deeper examination reveals significant similarities in operating principles, justification mechanisms, and societal effects.
One of the most central similarities is the incremental development and normalisation of systems. Nazi Germany's surveillance apparatus did not emerge overnight but developed in stages. Initially, seemingly harmless measures were introduced, such as the census, followed by gradually broader restrictions and surveillance mechanisms. The same pattern is visible in modern surveillance systems: initially, limited systems are introduced for a specific legitimate purpose, but gradually their scope expands and deepens.
Security rhetoric as a justification for surveillance
Another key similarity lies in the rhetoric used to justify these systems. "Public safety" has historically served as an effective justification for increasing surveillance. In Nazi Germany, after the Reichstag fire, the "Decree for the Protection of the People and State" was issued, revoking constitutional rights in the name of security. In current systems, the threat of terrorism and national security serve as equivalent justifying factors, enabling the restriction of fundamental rights.
The erosion of domestic privacy, then and now
The erosion of domestic privacy offers a concrete example of this continuum. In Nazi Germany, "preventive home searches" began immediately after the Reichstag fire. These searches initially targeted political opponents but gradually expanded to cover Jews and other "suspicious" groups. This activity was not based on concrete criminal suspicion but on preventive logic. The same principle is visible in current legislative changes, as authorities gain the right to breach domestic privacy in the name of "security inspections" without criminal suspicion.
Risk profiling and preventive surveillance
The creation of risk profiles and preventive surveillance is another key parallel between historical and modern systems. Nazi Germany used the punch card system to create "risk profiles" of different population groups. These profiles were based on individuals' characteristics, social connections, and historical data. Today's algorithmic profiling follows the same logic but employs more advanced mathematical models and vastly greater volumes of data. In both cases, the system defines a person's risk level and the corresponding level of surveillance before any concrete events have occurred.
The principle of data cross-referencing
The cross-referencing of data from various sources was a central feature of Nazi Germany's intelligence system. The Gestapo had an "integrated database" that combined information from various authorities, informants, and surveillance. Current civil and military intelligence laws similarly enable the cross-referencing of data from different sources, creating a comprehensive surveillance system. The difference is primarily in the volume of data and the speed of processing, not in the fundamental principle.
The illusion of legality as a justification for surveillance
The illusion of legality also connects both systems. Nazi Germany's surveillance apparatus was technically based on "lawful" decrees and regulations that had been enacted through proper channels — under emergency conditions, admittedly. This created an illusion of legality that facilitated the acceptance of the system. Current legislative changes operate in the same way: they create a "legal" basis for action that in practice enables the expansion of surveillance.
Technological differences and the invisibility of surveillance
Technological differences are obvious but do not change the fundamental principles. Implementing Nazi Germany's systems required physical presence and considerable manpower. Home searches, data collection, and analysis were laborious processes. Modern digital systems enable remote surveillance and automatic data analysis, making surveillance less visible and more cost-effective. This difference makes modern surveillance partly more dangerous, as the invisibility of surveillance reduces resistance to it.
The expansion of surveillance: A historical example
The home searches conducted in Berlin's Bayerisches Viertel between 1938 and 1942 provide an illustrative example of the similarity between these systems. These searches proceeded in three phases: first targeting Jews, then homes of "mixed marriages," and finally those Germans suspected of helping Jews. This gradual expansion illustrates the general trajectory of surveillance systems: they begin with a limited target and gradually expand to encompass an ever-greater share of the population.
The reduction of humans to numbers
The view of humanity inherent in surveillance systems also reveals a key similarity. Nazi Germany's system reduced people to numbers and categories that determined their value and treatment. Modern algorithms operate in the same way: they define an individual's value and rights on the basis of data points. In both systems, technical rationality replaces human judgement, leading to dehumanisation.
The visibility of surveillance and the challenges of resistance
There is a noteworthy difference between the systems in their visibility. Nazi Germany's surveillance was visible and overt: Jews were marked with the Star of David, home searches were public, and the presence of surveillance was obvious. Modern surveillance, by contrast, is often invisible: digital monitoring takes place in data networks, algorithmic decision-making is opaque, and the full picture of surveillance remains beyond the comprehension of most citizens. This invisibility makes resistance more difficult and the normalisation of surveillance easier.
Social trust and the erosion of community
At the societal level, both systems lead to the erosion of trust. Nazi Germany's informant system turned neighbours and friends into potential threats, destroying the foundation of social trust. Modern digital surveillance leads to the same outcome, but more subtly: the knowledge of constant surveillance makes people guard their words and actions, eroding the foundations of an open society. In both cases, the result is the weakening of community.
Minorities as targets of surveillance
The position of minorities within surveillance systems also connects these eras. Nazi Germany's system specifically targeted Jews, Roma, and other minorities. Modern surveillance technologies, particularly AI-based systems, often contain inherent biases that lead to the overrepresentation of minorities in "risk profiles." This algorithmic discrimination repeats historical patterns of discrimination, albeit in a new technological form.
"For there is nothing covered, that shall not be revealed; neither hid, that shall not be known. Therefore whatsoever ye have spoken in darkness shall be heard in the light; and that which ye have spoken in the ear in closets shall be proclaimed upon the housetops" (Luke 12:2–3, KJV). This passage takes on new meaning in the age of surveillance. It reminds us that as systems seek to conceal their true nature, the truth about their operations and effects will ultimately come to light. This applies to Nazi Germany's surveillance apparatus, whose horrors were revealed after the war, as much as to modern systems, whose true scope is gradually being exposed.
The position of children within surveillance systems
Children occupy a particularly concerning position in both systems. In Nazi Germany, children were raised to inform on their parents and accept state surveillance as a normal part of life. Today, surveillance technology is embedded in school systems and in the applications children use daily. This normalises surveillance for a new generation in a way that shapes their understanding of privacy and freedom.
The universal dynamic of power and technology
The greatest similarity between these systems is the unchanging human tendency to use power and technology as instruments of control. This tendency transcends political systems and ideologies. It manifests in totalitarian dictatorships and democratic societies alike, though to differing degrees and in different forms. It reflects a deeper truth about human nature and the dynamics of power — a truth whose recognition is essential to avoiding the repetition of history's mistakes.
These parallels do not mean that modern democratic societies are morally equivalent to Nazi Germany. Such a claim would be inaccurate and would diminish the singular evil of the Holocaust. Rather, the comparison reveals structural and functional similarities that help us understand the general principles governing surveillance systems and identify the risks associated with them.
The development pattern of surveillance systems
In the development of surveillance systems, a certain universal pattern can be identified that transcends historical and cultural contexts. This pattern typically begins with the identification of some crisis or threat, followed by an expansion of surveillance powers on the basis of the exceptional situation. These powers remain in force even after the crisis has passed, however, and gradually expand to encompass an ever-greater share of the population and its activities. Eventually, surveillance becomes part of normal daily life — an unquestioned element in the structure of society.
The Reichstag fire in Nazi Germany parallels the 9/11 terrorist attacks in our time. Both events led to significant changes in surveillance powers by invoking national security. In both cases, laws enacted in exceptional circumstances have become permanent. This demonstrates how difficult it is to revoke powers once granted, and how crises serve as catalysts for the expansion of surveillance.
Economic interests as drivers of surveillance
The intertwining of economic and political interests also connects both eras. Companies profited economically from the construction of Nazi Germany's surveillance systems. Similarly, today's technology companies profit from building surveillance infrastructure around the world. This economic interest creates a powerful incentive to develop and expand surveillance technologies regardless of their societal impact.
New technology has therefore not changed the fundamental logic of surveillance — only its scale and efficiency. The same principles that guided Nazi Germany's surveillance system are also visible in today's digital surveillance systems. This continuity reminds us that technological development does not in itself resolve the moral and societal problems associated with surveillance. On the contrary, it often only reinforces existing dynamics of power and control.
The fallacy of "I have nothing to hide"
The notion that "if I have nothing to hide, I have nothing to fear" appeared both during the Nazi era and in today's debate. This thinking is based on a fundamental misunderstanding of the meaning of privacy. Privacy is not merely the protection of secrets but the foundation of personal autonomy and human dignity. The loss of privacy gradually leads to self-censorship and the adjustment of behaviour to conform to presumed expectations.
Surveillance and prophetic dimensions
In both historical and modern surveillance systems, parallels can be observed in relation to religious prophecies. It is particularly noteworthy how the Book of Revelation's descriptions of control systems (such as Rev. 13:16–17) are finding concrete technological counterparts in current digital systems. A more detailed analysis of these prophetic dimensions can be found in Chapter 13, which examines the connection between the prophecies of Revelation and the development of surveillance technology in greater depth.
The real threat of surveillance technology
Ultimately, this comparison demonstrates that the greatest threat posed by surveillance technology lies not in the technology itself but in how it reshapes our understanding of humanity, freedom, and society. In the case of both Nazi Germany and modern surveillance systems, the real danger is the reduction of the human being to a standardised data object that can be measured, classified, and controlled. This reductionist view of humanity stands in fundamental conflict with the belief that every human being is a unique and valuable image of God, possessing inalienable worth and freedom.
The age of discernment calls us to recognise these continuities and make conscious choices in relation to surveillance technology. It calls us to ask which systems truly serve human flourishing and which restrict it. It calls us to consider how the possibilities of technology can be harnessed while simultaneously resisting its use as an instrument of control and oppression. These questions are not merely technical but profoundly moral and spiritual, and their answers will partly determine the direction of the future.
6. CHINA: THE PROTOTYPE OF THE MODERN SURVEILLANCE SOCIETY
A laboratory of digital control
China's surveillance system represents a historically unique stage in the technological implementation of societal control. It is not merely a theoretical model but a functioning, large-scale system that combines a traditional authoritarian governance structure with modern digital technology. China currently serves as a kind of laboratory in which surveillance technologies are being applied at full scale in a way that surpasses previous historical examples in both scope and intensity.
Historical background: The Hukou system
China's surveillance system is founded on a long history of centralised population registration. The Hukou system, which regulates citizens' place of residence and movement, was introduced as early as the 1950s. This system resembles Nazi Germany's identity card system in its principles, but it has evolved over decades into a comprehensive digital infrastructure. Hukou forms the foundation upon which more modern surveillance technologies are built, providing an established method for classifying and controlling the population.
The surveillance camera network
Particularly in the 2010s, China's surveillance system has advanced significantly. By current estimates, China has approximately 600 million surveillance cameras in operation — nearly one camera for every two citizens. This density significantly surpasses the surveillance camera systems of any other country. The cameras are not merely passive recorders but active identification systems that use facial recognition algorithms for real-time identification of individuals.
Xinjiang: The total surveillance laboratory
Xinjiang provides a concrete example of how this surveillance system operates at full scale. In this province in northwest China, home primarily to Uyghur Muslims, the world's most comprehensive surveillance infrastructure has been built. The system contains several components:
Facial recognition systems have been calibrated to identify Uyghurs specifically by ethnic appearance. This ethnic profiling is integrated into algorithms that continuously scan surveillance camera feeds. The system identifies individuals and classifies them by ethnic origin, enabling the systematic monitoring of the Uyghur population.
Checkpoints have been densely placed throughout cities and villages. At these points, citizens must identify themselves digitally, scan their faces, and often their phone contents as well. These checkpoints create a comprehensive network that tracks movement and social contacts in real time.
Biometric data is collected during compulsory "health examinations" in which DNA samples, iris recognition data, voice samples, and fingerprints are recorded. This data is fed into a centralised database that enables multi-faceted identification in various situations.
AI algorithms continuously analyse behaviour to identify "suspicious activities." The system detects deviations from normal behaviour — such as unusual movement patterns, social contacts, or spending behaviour — and flags them as potential risks.
Biometric surveillance as invisible marking
In many respects, this system resembles the surveillance Nazi Germany directed at Jews, but it is technologically far more advanced. Where Nazi Germany marked Jews with a yellow star and tattooed numbers on concentration camp prisoners, China uses biometric identifiers that function as an invisible yet all-pervasive marking system.
Although Xinjiang's system is an extreme example, the same technologies are gradually spreading across all of China. By 2020, it was estimated that China's facial recognition systems were capable of identifying over 1.4 billion faces in real time. Such surveillance capacity surpasses IBM's punch card systems many times over. It creates a digital panopticon in which citizens are under constant, invisible observation.
Social credit scoring as a behavioural tool
The development of a social credit scoring system represents a new level of surveillance and control. This system, whose development began around 2014, combines data from multiple sources to create a comprehensive assessment of a citizen's "trustworthiness." The system evaluates:
Online activity, social media, and communications: what people say online, whom they communicate with, and what content they consume.
Economic behaviour and payment practices: purchases, loans, bill payments, and financial responsibility.
Movement and travel: where people go, when, and with whom.
Social relationships and networks: a person's contacts and their trustworthiness ratings also affect the person's own rating.
This system is a digital version of Nazi Germany's "political reliability" assessment system. The significant difference is that China's system uses automation and algorithms for classification rather than human analysts. This enables a scale of surveillance that would have been impossible in the mechanical era.
Concrete consequences of social credit scoring
The consequences of the social credit scoring system are tangible. A low score can lead to travel restrictions, slower internet connections, restricted access to education and the labour market, and social stigma. The system functions as an effective behavioural tool, as citizens modify their actions to avoid negative consequences. This corresponds to the description in Revelation 13:17 of a system in which "no man might buy or sell, save he that had the mark."
Digital payment infrastructure as a surveillance tool
A critical component of China's system is its digital payment infrastructure. China has transitioned to a nearly cashless society, with the vast majority of payments processed through digital platforms such as Alipay and WeChat Pay. These systems enable the monitoring and analysis of every transaction. When this data is combined with the social credit score, a comprehensive system of economic surveillance emerges.
The digital yuan, the digital currency developed by China's central bank, deepens this surveillance still further. Unlike Bitcoin and other cryptocurrencies, the digital yuan is fully under the central bank's control and enables real-time transaction monitoring. It can also include "programmable" features that restrict the use of money for certain purposes or at certain times. This creates an infrastructure that enables unprecedented economic control.
The role of Western companies in building surveillance infrastructure
Western technology companies have played a significant role in developing China's surveillance infrastructure. This complicity is reminiscent of IBM's role in building Nazi Germany's surveillance apparatus. For example:
The American company Thermo Fisher Scientific supplied DNA sequencing equipment used in collecting biometric data from Uyghurs. The company ceased sales only in 2019 under international pressure.
Technology companies such as Nvidia, Seagate, and Intel have supplied components and processors used in surveillance camera networks and AI training.
Microsoft has conducted AI research in collaboration with Chinese organisations, including those involved in developing surveillance technology.
This collaboration raises serious ethical questions. Companies often justify their involvement by arguing that technology itself is neutral and that they are not responsible for how it is used. This argument echoes IBM's rhetoric during the Nazi era, demonstrating how business interests often override ethical considerations.
The global export of surveillance technology
China's surveillance model is not remaining within China's borders. China is actively exporting its surveillance technology and governance model to other countries, particularly through the Belt and Road Initiative. Companies such as Huawei, Hikvision, and Dahua have supplied surveillance systems to dozens of countries in Asia, Africa, and Latin America. This technology export is often tied to loans and development aid, creating an economic incentive for its adoption.
Particularly concerning is that many of these systems are being installed in democracies that lack strong legal safeguards against surveillance abuse. For example, Ecuador, Kenya, and Serbia have adopted Chinese surveillance systems that utilise facial recognition and AI analysis. This development threatens to normalise comprehensive surveillance even in democratic societies.
The EU's contradictory relationship with China
The EU's relationship with China in this context is complex and contradictory. Many EU leaders have expressed admiration for China's economic efficiency and technological development, creating a tension with China's serious human rights violations. This ambivalence is reflected in EU policy:
The EU-China Comprehensive Agreement on Investment (CAI) was advanced significantly in 2020 despite the deterioration of China's human rights situation in Xinjiang, Hong Kong, and Tibet. The agreement progressed even though information about Xinjiang's surveillance system and "re-education camps" was already widely known.
French President Emmanuel Macron has emphasised economic cooperation with China and warned that the EU should not "follow America's" China policy. Such an attitude prioritises economic interests at the expense of human rights.
Former German Chancellor Angela Merkel fought for the EU-China investment agreement despite human rights concerns. This reflects the strong economic ties between German industry and China.
Uncritical admiration of China's "efficiency"
Particularly problematic is the tendency of EU leaders to admire China's "efficiency" without recognising that this efficiency is partly based on surveillance and control. Infrastructure projects such as high-speed railways and high-rise construction, as well as technological development and digitisation, are often presented as examples of China's success without critical analysis of the cost at which they were achieved.
The scope of human rights violations
China's human rights problems, about which EU leaders often remain silent, are severe and widespread. The treatment of Uyghurs in Xinjiang meets the criteria for genocide by many assessments. An estimated one million Uyghurs have been confined in "re-education camps" where they are subjected to forced labour, political indoctrination, and cultural assimilation. This, combined with pervasive surveillance and forced sterilisations, constitutes a systematic attack on Uyghur culture and identity.
The long-standing occupation of Tibet and cultural suppression continues. The demonisation of the spiritual leader the Dalai Lama, the persecution of Tibetan Buddhists, and the massive settlement of Chinese migrants in the region aim to alter the demographic structure and eradicate Tibetan culture. The systematic suppression of the Tibetan language and culture continues in the education system and public life.
The suppression of Hong Kong's democracy movement is the most recent example of China's authoritarian actions. The introduction of the National Security Law in 2020 has led to the large-scale silencing of opposition, the shuttering of the free press, and the gradual dismantling of Hong Kong's special status in violation of international agreements.
All these actions take place within a one-party system in which the Chinese Communist Party exercises absolute power. The regular imprisonment of dissidents, enforced disappearances, internet censorship, and lack of judicial independence are central features of the system.
The dilemma of economic interests versus moral principles
The EU's relationship with China reflects a broader moral and strategic dilemma: how to balance economic interests with values-based principles. This dilemma is also relevant to surveillance technology, as many EU countries are developing similar systems, albeit on a smaller scale and within a different legislative framework.
The EU's digital identity initiative (European Digital Identity Wallet) contains elements that technically resemble China's digital ID system. Although the goals and implementation differ, the technological infrastructure creates the potential for broader surveillance in the future. Similarly, the European Central Bank's digital euro resembles China's digital yuan in its operating principles, though its design emphasises privacy protection.
"For what is a man profited, if he shall gain the whole world, and lose his own soul?" (Matt. 16:26, KJV). This verse reminds us that economic gain is not a sufficient basis for abandoning moral principles. The EU's attitude toward China's surveillance model reflects this tension between material interests and moral values.
Choices in the age of discernment
In the age of discernment, the EU's technological and moral direction is decisive. The technological temptation to increase control through digital identification and surveillance systems is strong. Economic pragmatism tempts the prioritisation of trade relations at the expense of human rights. At the same time, gradual normalisation makes surveillance technologies more acceptable as their implementation occurs in the name of "security" or "efficiency."
China's model as warning and possible future
China's surveillance society provides a concrete example of what a fully developed digital control system looks like in practice. It is not a theoretical model but a functioning system that demonstrates how technology can enable unprecedented levels of control. This example serves both as a warning and as a possible vision of the future, depending on the decisions Western nations make regarding their own surveillance systems.
China's model reminds us that technological surveillance systems that begin as "innocent" or "efficient" solutions can transform into instruments of oppression. The historical analogy of IBM's punch card systems in Nazi Germany finds its continuation in China's current digital surveillance infrastructure. Although the contexts differ, both examples demonstrate how technology can enable systematic discrimination and oppression when moral and legal safeguards are absent.
The significance of choices for the future
Examining China's prototype does not mean adopting a fatalistic attitude toward the future of digital surveillance. On the contrary, it underscores the importance of conscious choices and strong institutional safeguards. The future of Western democracies depends partly on how they respond to the challenge posed by China's surveillance model: either by adopting similar practices or by developing an alternative model that combines technological advancement with respect for individual rights.
7. FINLAND'S CURRENT LEGISLATIVE INITIATIVES AS ENABLERS OF SURVEILLANCE
Recent changes in Finnish legislation form a body of work that systematically expands the surveillance powers of authorities. These changes are not occurring in a vacuum but are part of a global development in which security-focused rhetoric justifies restrictions on privacy. Examined individually, these legislative initiatives may appear limited and justified, but as a whole they create an infrastructure that enables large-scale population surveillance.
Amendment to Section 10 of the Constitution
Section 10 of the Constitution has served as one of the most important privacy protections in Finland. Amending it to grant authorities access to the domestic sphere without criminal suspicion represents a fundamental shift in the relationship between authorities and citizens. This change dismantles a central principle of the Western rule of law: the right to privacy and protection against arbitrary interference by the state.
Comparing this amendment to Nazi Germany's "Reichstag Fire Decree" is not an exaggeration. In both cases, constitutional rights are restricted in the name of security. After the Reichstag fire, the "Decree for the Protection of the People and State" was issued, revoking constitutional rights by invoking security. Finland's constitutional amendment follows the same logic, albeit in a more moderate form: national security is placed above individual rights.
With this constitutional change, authorities can gain access to homes in the name of "security inspections" or "preventive measures." In concrete terms, this means that inspections can be carried out in homes on the basis of mere suspicion or an algorithm-generated risk assessment. With modern technology, this can also mean remote surveillance, as a legal basis now exists for breaching domestic privacy.
The Civilian Intelligence Act
The Civilian Intelligence Act creates a legal basis for mass surveillance. It grants the Security Police broad powers for information gathering in the name of "national security." The term "national security" is defined so loosely that it enables virtually unlimited intelligence activity. The law contains three particularly significant elements:
First, cable intelligence enables the screening and analysis of all cross-border data communications. In practice, this means that a system similar to the NSA's PRISM programme can be established in Finland, collecting and analysing vast volumes of communications traffic. With advanced surveillance technologies, the content of millions of messages can be automatically analysed in search of "suspicious" patterns.
Second, the law enables the profiling and risk classification of citizens without concrete criminal suspicion. AI algorithms can assess citizens' "security risk" on the basis of various parameters. Through this preventive logic, the principles of the legal system change significantly, shifting the emphasis from reactive law to anticipatory control.
Third, the law enables intelligence to be directed at entire groups, not just individuals. This can mean, for example, the systematic monitoring of certain religious communities, political groups, or civil society organisations. Group-based surveillance is reminiscent of historical examples in which entire population groups have been placed under special surveillance.
The Military Intelligence Act
The Military Intelligence Act complements civilian intelligence by bringing in the capabilities of the defence forces and compelling the private sector to cooperate. The law obliges telecommunications operators to assist authorities in intelligence activities, which in practice means direct access to communications systems. This compulsory cooperation is reminiscent of historical examples in which the private sector was obliged to provide technology and infrastructure for surveillance.
Under the Military Intelligence Act, signals intelligence expands to cover domestic communications as well, not just cross-border traffic. This creates a comprehensive network in which both civilian and military intelligence monitor communications traffic. The law also enables computer network intelligence, which means access to information systems via remote malware. In practice, this means that authorities can use advanced surveillance tools in the name of "national security."
Amendment to the Police Act and biometric identification
The amendment to the Police Act, granting police access to the passport and identity card register, is significant when combined with modern facial recognition technology. This enables the identification of citizens from surveillance cameras, the use of biometric data in large databases, and automatic tracking and monitoring of movement. A more detailed description of these technologies can be found in Chapter 9, which covers the surveillance technologies available to Finnish authorities.
Through facial recognition, surveillance cameras can be used for automatic identification in public spaces. The system can also review recorded video material and identify individuals retroactively, enabling the mapping of movements and social contacts after the fact.
Expansion of Border Guard powers
The expansion of Border Guard powers complements the national surveillance network and connects it to international systems such as the EU's Frontex and international intelligence systems. Broader powers enable the sharing of data with EU agencies and the authorities of other countries, linking Finland into a global surveillance network.
The Border Guard's advanced biometric identification systems are part of the EU's border security system. These systems are used at Finland's borders, and the data is stored in shared databases. The Border Guard can more effectively monitor citizens' cross-border movement and share this data with other authorities as part of risk analysis.
The cumulative impact of legislative changes
Together, these legislative changes form a whole that enables a comprehensive surveillance system. This system extends from public spaces to private homes, from the physical world to the digital, from the national to the international, and from communications to social relationships. It creates an infrastructure for continuous monitoring that covers virtually all areas of life.
National security and counter-terrorism are often invoked to justify these legislative changes. These justifications are reminiscent of historical examples in which the expansion of surveillance was justified by external threats. In Nazi Germany, the threat of communism served as an equivalent justification for increasing surveillance, just as the threat of terrorism serves today.
What is concerning is the incremental nature of these legislative changes. Each change is presented as limited and justified, but together they form a whole that significantly alters the relationship between citizen and state. This incremental development is reminiscent of earlier historical examples of the construction of a surveillance apparatus, which also proceeded in stages, none of which individually provoked sufficient resistance.
"For every one that doeth evil hateth the light, neither cometh to the light, lest his deeds should be reproved" (John 3:20, KJV). This verse reminds us of the importance of transparency and the dangers associated with activity conducted in darkness. The invisible nature of surveillance systems and the concealment of their operations from public debate are signs that these systems fear critical scrutiny.
The role of the Constitutional Law Committee
Finland's Constitutional Law Committee has traditionally served as a watchdog for the protection of fundamental rights. However, recent decisions that have enabled significant restrictions on fundamental rights raise questions about the effectiveness of this oversight mechanism. The amendment to Section 10 of the Constitution in particular demonstrates that constitutional protections previously held as sacred can be altered by political decision.
All these legislative changes have occurred with relatively little public debate. Finnish society is characterised by strong trust in authorities, which has partly enabled the expansion of surveillance powers without significant resistance. This trust is a valuable societal resource, but it can also lead to a lack of critical assessment.
The technical implementation of surveillance
As a result of legislative changes, new technical systems have been developed for authorities to implement surveillance. These systems and their technical features are discussed in more detail in Chapters 9, 10, and 12. Here is a brief overview of the key systems enabled by the legislative changes:
The P-STUVE project (Police Electronic Secure Communications Services) is developing readiness for real-time facial recognition in public spaces. The project is also developing a mobile application for police that enables the biometric identification of individuals in field conditions and the immediate checking of their data across various registers.
The ERICA system in emergency services collects and stores data about callers, enabling the creation of personal profiles. The system uses AML (Advanced Mobile Location) technology, which automatically activates the phone's precise location data during an emergency call.
For communications intelligence, operators have been required to install special "tapping points" in telecommunications cables, to which authorities can connect their surveillance equipment. The technical implementation of these systems is discussed in more detail in Chapter 12.
Ethical assessment of the legislative changes
From the perspective of the age of discernment, these legislative changes place us in a situation where we must make significant choices in our attitude toward surveillance and privacy. Do we accept the restriction of freedoms in the name of security? Do we recognise the true scope and effects of surveillance? Do we prioritise comfort and a sense of security at the expense of personal autonomy?
"And ye shall know the truth, and the truth shall make you free" (John 8:32, KJV). This verse reminds us that true security and freedom are founded on truth, not on surveillance and control. Surveillance systems create an illusion of security while simultaneously restricting genuine freedom, which is founded on trust and truth. The age of discernment calls us to choose truth over illusion, even when it means discomfort and uncertainty.
8. EU INITIATIVES AS PART OF THE SURVEILLANCE TRAJECTORY
At the European Union level, numerous initiatives are underway that complement and expand national surveillance systems. These initiatives are often presented from the perspective of economic development, improved security, or administrative efficiency, but they also have significant surveillance-related dimensions. EU initiatives are particularly significant because they harmonise surveillance practices across the entire union and create standards that also affect national legislation.
Digital identity (EUDI Wallet)
The digital identity (EUDI Wallet) is one of the EU's most central initiatives, set to significantly affect the lives of Europeans. The European Digital Identity Wallet aims to create a centralised digital identity system for all EU citizens. The system combines identity documents, bank accounts, health data, and other official documents into a single digital wallet, enabling the identification of citizens both online and in the physical world.
The EUDI Wallet shares certain similarities with China's digital ID system (discussed in more detail in Chapter 6), although its development is guided by different principles. The EU emphasises privacy protection and voluntariness, but the system nonetheless creates an infrastructure that could enable broader surveillance in the future. Systems that are initially voluntary often become practically mandatory once they become essential for participation in society.
Centralising digital identity into a single system creates several risks:
- It enables more comprehensive monitoring of citizens' activities, as previously separate identities are unified
- It creates a "single point of failure" vulnerability: a breach of the system puts all identity-related data at risk
- It concentrates power in the hands of the system's administrators, creating an imbalance between the individual and institutions
The EU's official documents emphasise user control over their own data and strong data protection. In reality, the system's architecture enables broader use of data than is publicly stated. The planned technical implementation of the EUDI Wallet includes "back doors" for authorities that enable access to data in the name of national security or criminal investigation. These exceptions are broadly defined and may lead to broader surveillance than citizens are told about.
Central bank digital currencies (CBDC)
Central bank digital currencies (CBDC) represent another significant trajectory. The European Central Bank is currently developing the digital euro, which is comparable to China's digital yuan. Unlike decentralised cryptocurrencies such as Bitcoin, a CBDC is under the full control of the central bank, giving authorities new capabilities for transaction monitoring and control.
The digital euro would enable centralised monitoring and control of all transactions. Every purchase, sale, and transfer would be recorded in the system, creating a complete digital trail of an individual's economic activity. This data can be combined with other sources, such as location data or online behaviour, creating a comprehensive picture of a person's lifestyle and activities.
A particularly concerning feature of digital central bank money is its "programmability." The digital euro could contain restrictions on what money can be used for, when it can be spent, or who can use it. Such control could be more precise than current restrictions: for example, certain benefits could be designated for use only for specific purposes, or money could be "locked" in crisis situations. Although such features are presented favourably (for example, as a tool against the shadow economy), they create an infrastructure that enables significant economic control.
The decline in cash use would lead to a situation where all economic activity is visible to the authorities. Cash is the last anonymous payment method that enables transactions without a digital trail. Its disappearance would mean total economic transparency, which would disproportionately affect disadvantaged groups without access to digital services.
The digital euro would also create the possibility of economic exclusion. If a person were classified as "untrustworthy" — for example, because of opinions expressed on social media — their access to digital currency could theoretically be restricted or blocked entirely. This could lead to economic marginalisation and a controlled society.
Digital Services Act (DSA) and Digital Markets Act (DMA)
The Digital Services Act (DSA) and Digital Markets Act (DMA) form a third significant area in the EU's surveillance development. These regulations contain elements that to some degree resemble China's internet governance system, albeit in a milder form.
The DSA imposes obligations on online platforms for content moderation and the removal of "illegal content" within 24 hours. The problem is the vagueness of the definition of "illegal content" and the possibility of its expansion in the future. History demonstrates that such regulations are often expanded beyond their original purposes, particularly in crisis situations or under political pressure.
Algorithmic transparency requirements paradoxically create the possibility of greater surveillance. When authorities gain access to platforms' algorithms, they can also demand changes to them in ways that enable the discrimination of certain types of content or certain individuals. This can lead to "soft censorship," where certain viewpoints are not technically banned but their visibility is algorithmically restricted.
"Disinformation" countermeasures are particularly problematic because the definition of "disinformation" is subjective and changeable. Historically, views that challenge the prevailing narrative have often been labelled "disinformation" but have later proven to be accurate. This was particularly evident during the Covid-19 pandemic, when several views that were later shown to be correct were initially labelled "disinformation."
These regulations create an infrastructure that technically enables broader content control, resembling China's approach to internet governance (though at a different scale). Although the EU justifies these regulations with consumer protection and market balancing, the technical infrastructure itself creates the possibility of its use for other purposes in the future.
Regulation of biometric identification
The regulation of biometric identification at EU level is a fourth significant area of development. The EU's AI Act includes regulation of biometric identification systems, but its safeguards are limited. The regulation in principle prohibits real-time biometric identification in public spaces but includes significant exceptions to this ban.
The regulation contains exceptions that permit authorities to use biometric identification in the name of public safety — for example, in counter-terrorism, searching for missing persons, or investigating certain crimes. These exceptions are broadly defined and enable the expansion of biometric surveillance in the future, particularly in crisis situations.
Technically, the EU is developing similar biometric identification technologies to China, even though the regulatory framework differs. Facial recognition systems are spreading to EU cities as part of "smart city" initiatives, often without sufficient public debate about their impact on privacy and civil liberties.
The development of these biometric identification systems normalises the continuous surveillance of the population, even if the rules are initially stricter than in China. Normalisation is a gradual process: first the technology is deployed in limited situations, then its scope of application is gradually expanded, and eventually it is accepted as a normal part of the urban environment.
European travel information and authorisation systems
The European Travel Information and Authorisation System (ETIAS) and the Entry/Exit System (EES) form a fifth area of the EU's surveillance development. These systems monitor persons entering and leaving the EU, collecting biometric identifiers and travel information.
The EES system records the data of all third-country nationals crossing EU external borders, including biometric identifiers (fingerprints and facial images). This system creates a comprehensive database of border-crossing individuals and enables the monitoring of their movements.
ETIAS, in turn, requires visa-exempt travellers to pre-register and obtain authorisation before entering the EU. The system collects data about travellers and performs an automatic risk assessment based on algorithmic profiling. This profiling contains elements that may lead to discrimination on the basis of nationality, ethnic background, or other factors.
These systems integrate into a broader European information system architecture that also includes the Schengen Information System (SIS II), the Visa Information System (VIS), and Europol's information systems. This interoperability enables the sharing and combining of data across different systems, creating more comprehensive surveillance capability.
"A righteous man regardeth the life of his beast: but the tender mercies of the wicked are cruel" (Prov. 12:10, KJV). This verse reminds us that a just system cares for the weaker and more vulnerable as well. EU surveillance systems have a particularly strong impact on vulnerable groups such as refugees, immigrants, and minorities, who often face more intensive profiling and surveillance.
European passenger name record system
The European Passenger Name Record (PNR) system collects data on all air passengers, including travel route information, payment methods, contact details, and even meal preferences. This data is stored for five years and can be used to profile travellers. The PNR system enables the analysis of travel habits and uses algorithms to identify "suspicious" travellers, often on vague criteria.
EU-funded research into AI-based border inspection technologies is also concerning. The iBorderCtrl project developed a "lie detection system" that analyses micro-expressions during border inspections to identify potentially "dishonest" travellers. The scientific basis of such systems is questionable, and they may lead to discrimination and false identifications, particularly for ethnic minorities.
Through the Horizon 2020 programme, the EU has funded numerous surveillance technology development projects, such as ROBORDER (autonomous border surveillance robots), FOLDOUT (forest area surveillance), and COMPASS2020 (maritime surveillance systems). These projects represent the EU's drive to develop ever more comprehensive surveillance technologies that leverage AI, robotics, and automation.
The EU's technological approach
The EU's technological neutrality is also problematic. The EU's approach often focuses on regulating technology rather than questioning its necessity or its effects on society. This approach normalises the development and use of surveillance technology, assuming that proper regulation is sufficient to prevent abuse.
One of the most significant risks in the EU's surveillance initiatives is "function creep" — the gradual expansion of purpose. Systems developed for a limited purpose gradually expand into new applications. For example, surveillance methods developed for counter-terrorism often expand to cover ordinary crime and eventually even administrative infractions. This phenomenon has been observed in numerous previous surveillance technologies.
EU initiatives are often justified by the need to counter external threats such as terrorism, organised crime, or illegal immigration. This rhetoric creates an opposition between "us" and "them," justifying increased surveillance. Yet history demonstrates that surveillance systems are ultimately used for internal monitoring and citizen control as well.
The EU's relationship to other surveillance systems
Also concerning is the EU's drive to achieve "international leadership" in technology regulation. In practice, this leadership often means that the EU develops surveillance standards that then spread globally. EU standards are often seen as "golden mean" solutions between China's authoritarian model and America's corporate-driven model, but they still contain significant surveillance elements.
The impact of EU infrastructure on Finland's situation is considerable. As a smaller member state, Finland often implements EU systems and regulations more broadly than strictly necessary. Finland displays a tendency toward "gold-plating" of EU regulations, where national legislation goes further than EU directives require. This, combined with Finland's strong technological infrastructure, creates a particularly fertile environment for the deployment of surveillance technologies.
Comparison of EU and Chinese systems
When comparing EU and Chinese systems (discussed in more detail in Chapter 6), significant differences as well as concerning similarities can be observed:
-
Goals and values: The EU emphasises democracy, privacy protection, and human rights, while China emphasises social harmony, societal stability, and state control. These different values lead to different emphases in system implementation.
-
Openness: EU systems are generally more open and transparent than China's and are subject to stricter legal restrictions. China's systems operate with less oversight and fewer legal restrictions.
-
Voluntariness vs. compulsion: The EU often emphasises the voluntary nature of systems, while in China participation is generally compulsory. In practice, however, "voluntary" systems in the EU can also become de facto compulsory when they become essential for functioning in society.
-
Technological similarities: Alarmingly, there are significant technological similarities between EU and Chinese systems. Both are developing facial recognition, digital identity systems, social media surveillance, and digital currencies. The technological infrastructure is similar in many respects, even though its purposes and restrictions differ.
-
Gradual expansion: In both the EU and China, surveillance systems have expanded incrementally, beginning with limited applications and progressing toward more comprehensive systems. This gradual development makes it difficult to criticise the systems, as individual steps appear minor.
The challenges of the age of discernment
"While we look not at the things which are seen, but at the things which are not seen: for the things which are seen are temporal; but the things which are not seen are eternal" (2 Cor. 4:18, KJV). This verse reminds us that technological systems are temporary, but their effects on human dignity, freedom, and spiritual development can be far-reaching. The age of discernment calls us to examine these systems from a deeper perspective that transcends the visible technology and focuses on their spiritual and moral dimensions.
The history of humanity demonstrates that the forms of power change, but their underlying logic remains the same. The EU's surveillance initiatives represent a more modern, more subtle form of control than previous historical examples, but their ultimate purpose is the same: the steering of human behaviour, the centralisation of information, and the control of deviation. Recognising this logic of control in its modern form is a central part of the spiritual challenges of the age of discernment.
The central question of the age of discernment is how we relate to these evolving systems. Do we accept them uncritically in the name of efficiency and security, or do we evaluate them critically in the light of moral and spiritual principles? These choices determine not only the direction of our societies but also our own spiritual development.
9. SURVEILLANCE TECHNOLOGIES AVAILABLE TO FINNISH AUTHORITIES
The surveillance capabilities of Finnish authorities have developed significantly in recent decades. This development has been both legislative and technological, but the pace of technical advancement has often left legislation and public debate behind. Finnish authorities now use many advanced surveillance technologies, some of which come from foreign, particularly Israeli, suppliers. The deployment of these technologies has often occurred without broad public debate about their impact on privacy and civil liberties.
Israeli surveillance technologies
Israeli surveillance technologies form a significant part of the toolkit available to Finnish authorities. Israel has developed some of the world's most advanced surveillance systems, partly due to its geopolitical position, and these technologies are actively exported around the world, including to Western countries. The presence of Israeli surveillance technologies in Finland raises questions about the origin of the technology, its intended uses, and its ethical dimensions.
Cellebrite
Cellebrite is one of the best-known Israeli surveillance technology companies whose products are used by Finnish authorities. The National Bureau of Investigation (KRP) and local police use Cellebrite's UFED (Universal Forensic Extraction Device) equipment for digital forensics. These devices are powerful tools that enable the extraction of data from mobile devices, including locked phones.
UFED devices are capable of bypassing PIN codes, patterns, and biometric protections; recovering deleted data; and extracting encrypted application data. In practice, this means that authorities can obtain virtually all data stored on a phone, including messages, photos, application data, browsing history, and location data, even if the data has been encrypted or deleted.
Cellebrite's Physical Analyzer software analyses data obtained from phones and reconstructs the user's activity. It creates a timeline and location history, identifies social networks through contacts and communications, and visualises data in an easily understandable format. This enables comprehensive mapping of a person's digital life.
UFED Cloud Analyzer retrieves data from cloud services such as Google Drive, iCloud, and Dropbox. It uses login credentials found on the device to access cloud data, extending data collection beyond the phone itself. This technology enables access to data not stored on the physical device, which is particularly significant in today's era of cloud services.
Finnish Customs also uses Cellebrite technology to analyse seized devices. This is publicly known and has been mentioned in Customs' own publications and procurement information. The use of Cellebrite technology in Finland is an example of how advanced surveillance technology has been normalised as part of authority operations without broad public debate about its impact on privacy.
Verint Systems
Verint Systems is another Israeli company whose systems Finnish authorities may use. Verint's systems are wide-ranging surveillance solutions that enable comprehensive analysis of communications traffic. Finnish intelligence authorities, particularly the Security Police, may have acquired Verint Systems' communications analysis systems as part of the modernisation of signals intelligence.
Verint's "Voice Mining" system can be used for speech recognition and analysis. It automatically identifies speakers through voice recognition, conducts keyword searches on calls, and identifies conversations of interest. The system uses AI to identify emotional states and signs of stress in speech, enabling deeper analysis of voice communications.
Horizon VM and other Verint systems enable surveillance that exceeds the boundaries of traditional wiretapping. They not only record communications but analyse them automatically and identify patterns and anomalies. This automatic analysis enables broader surveillance with fewer personnel resources, making mass surveillance technically and economically feasible.
NSO Group's Pegasus
There is no confirmed public information about the use of NSO Group's Pegasus software in Finland. The Pegasus Project investigation by Amnesty International and other human rights organisations has not found indications of Pegasus use in Finland. Finnish legislation places significant restrictions on the use of such systems, but new intelligence legislation has made their use theoretically possible in certain national security situations.
It should be noted, however, that even if Pegasus is not in use, other similar, less well-known systems may have been acquired. It is known that several Western countries use technology from companies like NSO, even though this is not publicly acknowledged. This uncertainty reflects the lack of transparency in the use of surveillance technology.
Unit 8200
Unit 8200 is the Israeli military's intelligence unit, which has developed many surveillance technologies now in commercial use. Although Finland does not directly "procure" technology from a military unit, the connections manifest more indirectly. Many of the Israeli intelligence and security technologies acquired by Finland were developed by former members of Unit 8200. For example, the founders of Cellebrite and possibly other Israeli surveillance technology companies used in Finland have backgrounds in this unit.
The Finnish Defence Forces and the Cybersecurity Centre engage in international cooperation, with Israel as one partner, particularly in the field of cybersecurity. This cooperation may include information exchange and possibly technical collaboration related to surveillance technologies. However, only limited public information is available about the nature and scope of such cooperation.
Clearview AI
Clearview AI represents a different but equally significant development in surveillance technology. Unlike Israeli companies, Clearview AI is an American company founded by Hoan Ton-That in 2017. It has developed a facial recognition system that has attracted worldwide attention and concern.
Clearview AI's operating principle is based on a vast database. The company has collected over 10 billion facial images by "scraping" them from social media, news sites, and other public sources without user consent. This vast database is compared against images submitted by authorities in the identification process. The system is capable of identifying individuals even from partial facial images or in challenging lighting conditions.
Clearview AI's use in Finland is documented: the National Bureau of Investigation trialled the system without proper authorisation or data protection processes. This led to a reprimand from the Data Protection Ombudsman, and the KRP later announced it had discontinued use of the system. The case is significant, as it demonstrates Finnish authorities' interest in advanced surveillance technologies even when legal and ethical questions remain unresolved.
Due to European data protection regulations (GDPR), the use of Clearview AI in Europe is problematic, and many EU countries have imposed fines on the company and banned its use. Clearview AI represents a significant challenge to privacy: it combines publicly available information in a way that enables the identification of almost anyone in public spaces. Such technology fundamentally changes our understanding of anonymity in public.
Multi-biometric identification
The development of multi-biometric identification in Finland represents a significant step toward more comprehensive biometric surveillance. The project led by the National Police Board replaces the police's old AFIS (Automated Fingerprint Identification System) with a new, significantly more advanced system that combines multiple biometric identifiers.
The name "multi-biometric identification" reveals an essential change: whereas the old system focused solely on fingerprints, the new system combines multiple biometric identifiers such as fingerprints, facial images, and potentially also iris recognition, voice recognition, and gait recognition.
The technical details of multi-biometric identification are partly classified, but the system likely includes automatic facial recognition that can work in conjunction with surveillance camera systems, an AI-based identification algorithm that improves the identification rate by combining different biometric data, and the ability to use identification on a broader group, not just criminal suspects.
Such a system enables significantly more effective monitoring and identification than mere fingerprint comparison. Collecting fingerprints requires physical contact or a trace, limiting its use. Facial images can be collected remotely, unobtrusively, and on a mass scale. Combining multiple biometric identifiers reduces errors and increases identification accuracy.
The P-STUVE project
The P-STUVE project (Police Electronic Secure Communications Services) is another overlooked but significant reform. As part of the project, the police are developing readiness for real-time facial recognition in public spaces — not limited to criminal suspects, but theoretically capable of identifying anyone in a public place.
P-STUVE also includes an expansion of field applications. The project is developing a mobile application for police that enables the biometric identification of individuals in field conditions (face, fingerprints) and the immediate checking of data across various registers. This significantly expands the police's ability to identify and profile individuals while on the move.
The system also includes an AI-based component that aims to predict crime geographically and target surveillance accordingly. This predictive policing resembles the predictive systems developed in Israel that seek to identify potential threats before anything concrete has occurred.
It is noteworthy that the P-STUVE project involves Israeli technology and expertise, although this connection is not usually highlighted in public materials. This once again reflects the significant role of Israeli surveillance technology in developing Finland's surveillance infrastructure.
Finland's role in international signals intelligence
Finland also plays a significant role in international signals intelligence. The Defence Forces' Intelligence Division maintains systems that monitor signals emanating particularly from Russia. These systems have been developed in cooperation with Western intelligence services and share information as part of an international network.
According to the Snowden revelations, Finland has an arrangement called SUSLAG (a signals intelligence data exchange agreement between Finland and the United States), through which Finnish intelligence shares Russian communications traffic data with the NSA in exchange for advanced surveillance technologies. This cooperation demonstrates that Finland is not merely a user of surveillance technology but also an active participant in international intelligence cooperation.
Other surveillance systems
Finland also has other surveillance systems in operation, whose technical details are discussed in more detail in Chapters 10 and 12:
- The ERICA system, which collects and stores data about individuals calling emergency services
- Communications intelligence infrastructure in telecommunications operator networks
- The Digisyke project for real-time collection of health data
- Public transport travel card data and movement tracking
- Data collected by banks and financial institutions on financial transactions
The practical effectiveness of surveillance systems
The practical effectiveness of these systems is illustrated by the Krista Kiuru case in December 2024, in which the perpetrator was identified and apprehended extremely quickly. This case is examined in more detail in Chapter 11, which analyses how the systems worked together in the investigation of a high-profile case. The case demonstrates that Finland's surveillance systems are sophisticated and effective, particularly when high-profile events are involved.
"I the LORD search the heart, I try the reins, even to give every man according to his ways, and according to the fruit of his doings" (Jer. 17:10, KJV). This verse reminds us that only God has the right to see into a person's innermost being. Modern surveillance systems, however, seek to imitate this ability, creating the illusion of digital "omniscience" that is fundamentally an imitation of a divine attribute.
Integration of government information systems
The integration of government information systems is a significant development in Finland's surveillance capacity. Traditionally, different authorities' information systems have been separate, limiting the combining of data and large-scale surveillance. Current development, however, aims to integrate these systems, enabling faster and broader sharing of data between authorities.
Such integrated systems enable the creation of comprehensive personal profiles by combining data from different authorities. Police, Customs, the Border Guard, and the Security Police can share data more effectively than before, creating a more comprehensive picture of surveillance targets. This combining of data can occur more easily than before under the new legislation.
The integration of government systems is advanced by AI-based components that identify "anomalies" in normal behaviour. These systems can automatically flag individuals whose activity deviates from what is expected. This predictive logic changes the nature of surveillance from reactive to anticipatory, raising questions about legal protections and human dignity.
The role of commercial actors
The Finnish state also has access to commercial surveillance technology. This includes systems for monitoring network traffic, social media analysis tools, and location technologies. The use of these technologies is often less regulated than official surveillance systems, enabling a "grey area" of surveillance that does not fully fall within the scope of traditional government surveillance.
The perspective of the age of discernment
From the perspective of the age of discernment, the development of these surveillance technologies poses significant moral and spiritual challenges. We must ask to what degree the use of these systems is justified, where the boundary of acceptable surveillance lies, and how technological development affects our understanding of human dignity and freedom.
"Ye have heard that it hath been said, An eye for an eye, and a tooth for a tooth: But I say unto you, That ye resist not evil" (Matt. 5:38–39, KJV). This verse reminds us that our response to technological surveillance should not be based on fear or hatred but on wisdom and truth. We must recognise the real effects of these systems on society and the individual, but do so in a spirit of love and truth.
Ultimately, it is about what kind of society we want to build. Surveillance technologies are tools that can be used for both good and ill. Their moral value depends on how they are used and on the values on which they are developed. The age of discernment calls us to evaluate these technologies critically, recognising their potential dangers but also their potential to promote a more just and secure society.
We cannot flee the advance of technology, but we can influence how it shapes our society. This requires open debate, transparency in decision-making, and a firm commitment to ethical principles. In the age of surveillance technology, the time of discernment calls us to defend human dignity and freedom in the midst of technology — not so much by opposing technology itself, but by ensuring that it serves humane and moral ends.
10. LITTLE-KNOWN SURVEILLANCE SYSTEMS AND INITIATIVES IN FINLAND
Although public debate about Finland's surveillance capabilities often focuses on the most visible systems and legislative changes, many significant surveillance systems and initiatives receive little attention. These systems often operate quietly in the background, collecting and analysing large volumes of data about citizens. To form a comprehensive picture, it is important to examine these lesser-known systems as well, which together form a significant part of Finnish society's surveillance infrastructure.
Finland's role in international signals intelligence
Finland's role in international signals intelligence is considerably more significant than is generally recognised. Finland's geopolitical position as Russia's neighbour makes it an especially attractive partner for Western intelligence services. The Defence Forces' Intelligence Division maintains advanced signals intelligence systems that focus particularly on monitoring signals emanating from Russia.
Of particular significance is the signals intelligence centre in Santahamina, which is rarely mentioned in public debate. This centre is part of a broader international intelligence network, and its technological infrastructure has been partly developed through international cooperation. The centre's activities extend beyond traditional military intelligence, and the data it collects can also be used in civilian intelligence.
Edward Snowden's revelations in 2013 pointed to a cooperative arrangement called SUSLAG between Finland and the United States' National Security Agency (NSA). Through this arrangement, Finland shares Russian communications traffic data with the NSA in exchange for advanced surveillance technology. This cooperation gives Finland access to world-class surveillance technology that it could not otherwise develop, but it simultaneously ties Finland into a global surveillance network.
The development of Finland's signals intelligence systems has followed global trends, moving toward increasingly automated data collection and analysis. Modern systems do not merely store data but analyse it in real time using advanced algorithms. This enables the screening of large volumes of data and the automatic identification of "interesting" signals.
The ERICA emergency response system as a surveillance tool
The emergency services' ERICA system is another initiative that has received little attention but has significant surveillance dimensions. ERICA (Emergency Response Integrated Common Authorities) is an emergency centre system that was deployed in Finland in 2018. Its official purpose is to improve the efficiency of emergency centre services, but the system also has less visible features.
ERICA collects and stores data about callers in a way that enables the creation of personal profiles. The system identifies repeat callers and automatically generates risk assessments for them. These profiles can affect how authorities respond to future contacts, creating a kind of algorithm-based classification system for citizens.
Particularly significant is ERICA's use of AML technology (Advanced Mobile Location), which automatically activates the phone's precise location data during an emergency call. This technology can locate a caller with accuracy up to 5 metres, which is considerably more precise than traditional location methods. This location data is stored in the system and can be used later for other purposes.
ERICA also functions as an interface through which emergency services, police, and healthcare share data. This data sharing often occurs without clear restrictions on the purposes for which the data may be used. Data collected through ERICA can thus end up being used more broadly than citizens assume when calling emergency services.
The physical infrastructure of communications intelligence
The physical infrastructure of communications intelligence is perhaps one of the least known but technically most significant components of Finland's surveillance system. Following the 2019 intelligence laws, Finnish telecommunications operators acquired a legal obligation to install special "tapping points" in telecommunications cables, to which authorities can connect their surveillance equipment.
These tapping points have been installed at key nodes in the telecommunications network, particularly at points where data traffic crosses Finland's borders. Technically, these are "splitter"-type solutions that copy part of the data traffic for analysis by authorities. This infrastructure enables large-scale monitoring of data traffic without ordinary users noticing anything unusual.
Advanced systems are used for screening data traffic, searching for keywords, communication patterns, and other "interesting" signals. These systems are capable of processing large volumes of data in real time and identifying algorithmically defined subjects of interest. Contrary to common assumptions, the system is not merely reactive but is also capable of identifying anomalies and unusual behavioural patterns.
Particularly concerning is that data captured by communications intelligence is stored in long-term databases whose retention periods are considerably longer than publicly disclosed. This enables the analysis of historical data and the construction of profiles over long time periods, making the system an even more powerful surveillance tool.
The Digisyke project and health data surveillance
The Digisyke project is one of the least known but potentially most broadly impactful surveillance initiatives in Finland. This project aims at real-time collection of health data from Finnish citizens, combining Kanta system data, data collected from wearable devices, and other health-related information.
The Digisyke system includes an AI-based component that assesses an individual's health risks on the basis of accumulated data. This enables anticipatory intervention in which health authorities' actions can be targeted at individuals assessed to be at risk for certain health problems. Although this is justified by improving public health, it simultaneously creates a new level of health surveillance.
Particularly problematic is that Digisyke data is available more broadly than is generally assumed. Although healthcare data should be strictly protected, the system enables data sharing not only with healthcare professionals but also, in certain cases, with social services, insurance companies, and other authorities. The restrictions on data use are in practice looser than the legislation would suggest.
Health data surveillance is a particularly sensitive issue, as health data is among the most intimate and personal information that can be collected about a person. A system that enables broad access to this data and its algorithmic analysis creates a new form of biopolitical surveillance in which health becomes a subject of surveillance and control.
Public transport movement data collection
The collection of public transport movement data in Finland is another form of surveillance that has received little attention. Travel card data from HSL and other transport operators provides detailed information about citizens' movements. This data is collected and retained for considerably longer than most users realise.
Data collected from travel card usage enables detailed analysis of an individual's movement patterns. The system records when and where a person boards and exits a vehicle, enabling the tracking of movement in time and space. This data can be combined with other sources to create a more comprehensive picture of an individual's movements and routines.
WHIM and other MaaS (Mobility as a Service) applications collect even more detailed information about users' movements. These applications continuously track the user's location, analyse movement habits, and create user profiles. This data is available to authorities when needed without a separate authorisation process, through "security cooperation," creating a new level of movement surveillance.
Public transport camera surveillance is also evolving. HSL and other operators have deployed advanced camera surveillance systems with integrated facial recognition capability. This enables the identification and tracking of passengers throughout the entire travel chain, which combined with travel card data creates a comprehensive picture of a person's movements.
The surveillance role of banks and financial institutions
Data collected by banks and financial institutions constitutes one of the least known but potentially broadest forms of surveillance. Finnish banks use advanced algorithms that identify "unusual" payment behaviour patterns. These algorithms do not merely monitor large or suspicious payments but comprehensively analyse an individual's economic behaviour.
Significantly, there exists a near-real-time data exchange system between banks and authorities that does not always require separate authorisation for data disclosure. The system operates particularly through the Financial Intelligence Unit, but in practice data can be shared through it for other purposes as well. This enables comprehensive monitoring of citizens' economic activity.
Special monitoring of cash use is also part of this system. Cash use is now subject to particularly close monitoring, and even relatively small cash withdrawals or deposits can trigger automatic notification to authorities. This development steers citizens toward digital payment methods, which are more easily monitored and traceable.
"For though we walk in the flesh, we do not war after the flesh: (For the weapons of our warfare are not carnal, but mighty through God to the pulling down of strong holds;)" (2 Cor. 10:3–4, KJV). This verse reminds us that resistance to surveillance systems occurs not primarily through technological means but through spiritual vigilance and the speaking of truth. Truth itself is the most powerful weapon in exposing invisible surveillance systems.
Integration of government information systems
One little-discussed dimension is the integration and cross-referencing of different surveillance systems. Traditionally, different authorities have had separate systems, which has limited data combining and comprehensive surveillance. The current development trend, however, seeks to break down these silos and create integrated systems that enable data sharing across different authorities.
Finland is developing shared government information systems that enable different authorities to access each other's data. These systems connect the databases of the police, Customs, the Border Guard, and the Security Police, enabling the creation of comprehensive personal profiles. Such a profile combines a person's criminal records, border crossing data, tax data, social media analyses, and other data sources to create a comprehensive picture of the individual.
Particularly concerning is the use of AI in these integrated systems. Advanced algorithms analyse data and automatically identify "interesting" individuals or behavioural patterns. This algorithmic surveillance occurs without direct human oversight, reducing transparency and accountability in the system's operations.
Government integrated systems also raise the question of the limits of data use. Once data is recorded in the system, it can be used for different purposes than those for which it was originally collected. This "purpose creep" is a common phenomenon in surveillance systems and leads to gradually broader use of data than originally planned or approved.
Data mining and network analysis tools
Data mining tools used by Finnish authorities are also little-known but significant instruments of surveillance. These tools analyse large volumes of data and identify patterns and connections that would be impossible to detect manually. Such analysis enables anticipatory action in which authorities can intervene in situations before any crime has even occurred.
Data mining is also used for network analysis, in which the connections and social networks between individuals are mapped. This enables "guilt by association" surveillance, in which individuals are monitored and profiled on the basis of their social contacts. Such surveillance is particularly problematic because it violates the presumption of innocence and leads to the profiling of people on the basis of factors they cannot control.
The cumulative impact of the surveillance network
The combination of all these systems produces a comprehensive surveillance network that extends to almost every area of life. This network monitors movement, communications, economic activity, health, and social relationships. It enables the creation of comprehensive profiles, predictive analysis, and subtle behavioural steering. Although the systems were developed separately and for different purposes, their combined effect is far greater than the sum of the individual parts.
Particularly concerning is the invisibility of these systems to the ordinary citizen. The vast majority of Finns are unaware of the existence or extent of these systems, making critical assessment and democratic oversight difficult. This lack of awareness also means that citizens do not know how to protect themselves from excessive surveillance or demand limitations on the operation of these systems.
The truth is that Finland has a considerably more advanced and extensive surveillance infrastructure in place than most citizens realise. This infrastructure is continuously developing and expanding, often without sufficient public debate or democratic oversight. Although the purpose of these systems is often acceptable, their combined effect can be concerning from the perspective of privacy and civil liberties.
"Therefore whatsoever ye have spoken in darkness shall be heard in the light; and that which ye have spoken in the ear in closets shall be proclaimed upon the housetops" (Luke 12:3, KJV). This verse reminds us that no surveillance is fully invisible and that the truth is ultimately revealed. In the age of discernment, our task is to make the invisible visible, so that society can make informed decisions about what kind of surveillance it considers acceptable.
The challenges of the age of discernment
The age of discernment calls us to evaluate these systems critically but wisely. We must recognise the systems' true objectives and effects, distinguish legitimate security activity from excessive surveillance, and defend privacy and freedom in the midst of technological development. This is not merely a technological or political question but a profoundly moral and spiritual challenge for our society.
11. THE KRISTA KIURU CASE — A DEMONSTRATION OF THE SURVEILLANCE SYSTEM'S EFFECTIVENESS
The assault on Krista Kiuru in December 2024 and the subsequent rapid identification of the perpetrator provide a concrete and timely example of the true capabilities of Finland's surveillance systems. By examining the case, we can see how theoretical capabilities translate into practical reality when authorities mobilise their resources to solve a "high-profile" case. At the same time, the case raises critical questions about the prioritisation of surveillance technology and societal justice.
The course of events
The course of events was clear. Member of Parliament Kiuru was attacked in a public place in Kaisaniemi park on Friday, 13 December 2024, and the perpetrator left the scene unidentified. An unknown man approached Kiuru while she was on her way to collect her child from nursery and struck her unexpectedly in the face with his fist. Police began their investigation immediately and arrested the suspect the following day, 14 December, in Vantaa. He was a 34-year-old man with a prior criminal history of similar offences. He admitted the act during questioning and said his motive was his belief that Kiuru was calling the police about his disruptive behaviour. Police found no indication of a political motive.
Surveillance technologies used in the investigation
Several advanced surveillance technologies were utilised in the Kiuru case, the technical features of which are discussed in more detail in Chapters 9 and 12. Here we focus on how these technologies were applied in practice in this specific case:
The surveillance camera network
A comprehensive surveillance camera network played a prominent role in the case. Public space cameras may have recorded the event, but in addition, authorities were able to use cameras from nearby commercial operators, traffic systems, and public infrastructure to map the perpetrator's movements. Kaisaniemi park is located near Helsinki railway station, which has Finland's most extensive camera surveillance. This extensive camera network practically enabled precise tracking of the perpetrator's movements.
Facial recognition technology
Facial recognition technology played a decisive role. The surveillance camera's recorded image of the perpetrator could be fed into a facial recognition system that compared it against databases available to authorities. These databases do not contain only criminal record data but also other material, such as passport photos, driving licences, and other official identification photos. The comparison quickly produced a set of possible matches, from which specialists identified the most likely perpetrator. This utilised the multi-biometric identification system described in Chapter 9.
Mobile network location data
The significance of mobile network location data in modern investigation is self-evident. To identify individuals present in the area at the time of the event, authorities can collect base station data showing whose phones were registered at base stations near the scene. This data, combined with other information, significantly narrows the pool of suspects.
Social media analysis
Social media analysis supplements more traditional forms of intelligence. Authorities use advanced algorithms to comb through public social media sources searching for references to the event and possible perpetrators. This analysis may reveal, for example, image material from the event, eyewitness observations, or possible posts by the perpetrator themselves.
Integrated system operation
A significant aspect is the integrated operation of different systems. The information systems of different authorities (police, Security Police) work seamlessly together, enabling rapid data sharing and analysis. This integration is a key factor in the effectiveness of surveillance systems, and the Kiuru case demonstrates that in Finland, this integration operates in near-real-time in high-profile cases.
"For there is nothing covered, that shall not be revealed; neither hid, that shall not be known" (Luke 12:2, KJV). This verse takes on new meaning in the age of modern surveillance technology. The Kiuru case demonstrates how difficult, if not impossible, it is to act undetected in a society where digital systems are continuously recording and analysing their surroundings.
Bypassing normal authorisation processes?
Noteworthy in the case is the possible bypassing of normal authorisation processes. When a high-profile individual such as a member of parliament is involved, the normal restrictions and authorisation procedures related to data acquisition and analysis can be set aside on grounds of "national security." This illustrates how surveillance powers expand in crisis situations, and how exceptions can become standard practice.
The case also contains elements of international cooperation. Finnish authorities may utilise international databases and cooperation partners in identifying perpetrators, particularly if there is reason to suspect international connections. This underscores how national surveillance systems are increasingly linked to global networks.
The effectiveness of technical surveillance and the perpetrator's profile
The Kiuru case reveals a truth about Finland's surveillance capabilities that goes beyond public discourse. In public debate, surveillance is often discussed as a theoretical possibility or a future development trend, but the Kiuru case demonstrates that these capabilities are already in use and functioning effectively. The speed of identification indicates that the system not only works but operates smoothly when sufficient resources are directed at it.
An important observation, however, is that the perpetrator was a 34-year-old man with an extensive criminal history, including multiple previous public-place assaults. He was very likely already well known to police, which partly explains the rapid identification. He had previously been convicted of dozens of offences and had been charged with assault six times. In May 2020, he had committed a series of assaults on the Espoo metro, striking three strangers and a security guard. This metro violence was captured on surveillance cameras.
The prioritisation of surveillance and inequality
The rapid resolution of the case generated a positive public response. Citizens and media praised the authorities' swift and effective action. This positive reaction is understandable — it was, after all, a serious offence whose perpetrator was quickly brought to justice. However, this reaction also reveals how surveillance systems become normalised in crisis situations, when they are perceived as working on the "good" side against the "bad."
It is, however, worth asking a critical question: why is the same technology and the same resources not used to solve crimes against "ordinary" citizens? When an ordinary person becomes the victim of a crime — whether robbery, assault, or another offence against the person — the resolution rates are considerably lower and the speed of investigation significantly slower. This reveals a deep element of inequality in the use of surveillance technology: the same broad capabilities that are mobilised immediately in high-profile cases are not deployed when the victim is an ordinary citizen.
Such inequality in the use of surveillance technology is both legally and morally problematic. It places citizens in an unequal position before the law and signals that the security and legal protection of some are more important than others. At the same time, it reveals the political nature of surveillance systems: they are not merely neutral tools for combating crime but systems whose use is prioritised according to the interests of power structures.
"If ye have not been faithful in that which is least, who will commit to your trust the true riches?" (Ancient wisdom). This wisdom reminds us that the credibility of a justice system is measured by its ability to treat everyone fairly, not just in special cases. The unequal use of surveillance technology undermines trust in the system as a whole.
The effectiveness of surveillance and system integration
The Kiuru case also demonstrates how central the integration of technology is to the effectiveness of modern surveillance. Individual systems — facial recognition, mobile monitoring, social media analytics — are effective, but their true power becomes apparent when they operate seamlessly together. This integration requires not only technical infrastructure but also an organisational culture that enables data sharing and cooperation between different actors.
It is also worth asking what the social costs of such effective surveillance are. Although the outcome in the Kiuru case appeared positive, the large-scale application of the system to all citizens could lead to significant losses of privacy and autonomy. These costs should be carefully weighed against the security benefits achieved, particularly considering that surveillance can also be used for political control and the silencing of dissent.
The sophistication of the surveillance infrastructure
The technical execution of the Kiuru case also reveals how advanced Finland's surveillance infrastructure truly is. Although Finland is not often perceived in public debate as a surveillance society, its technical infrastructure would enable very extensive surveillance if desired. This gap between public perception and technical capabilities is significant from the standpoint of democratic oversight — citizens cannot oversee systems whose existence or capabilities they are unaware of.
"And have no fellowship with the unfruitful works of darkness, but rather reprove them. For it is a shame even to speak of those things which are done of them in secret. But all things that are reproved are made manifest by the light: for whatsoever doth make manifest is light" (Eph. 5:11–13, KJV). This passage reminds us of the importance of transparency. The transparency and democratic oversight of surveillance systems are essential to prevent them from becoming instruments of arbitrary power.
A success story or a warning?
The Krista Kiuru case presents an interesting paradox: it is both a success story and a warning. A success story from a security perspective, as the perpetrator was quickly caught, but a warning about how effective and comprehensive Finland's surveillance system already is. This system would be technically ready for far broader use if political decisions enabled it or a crisis demanded it.
The case also raises the question of why ordinary citizens are not told more precisely about the systems by which they can be monitored. Authorities often invoke operational security as the basis for secrecy, but in a democratic society, citizens should have sufficient information about systems to which they are potentially subject. This transparency is essential for fundamental rights and democratic oversight.
Another significant lesson from the Kiuru case is how quickly normal restrictions and authorisation processes can be bypassed in a crisis. This "state of emergency logic" is a key mechanism in the expansion of surveillance: initially exceptional powers gradually become normalised, and eventually they become standard practice. The Krista Kiuru case demonstrates how swiftly and effectively this mechanism can work in practice.
The case also demonstrates how difficult it is to maintain anonymity in modern society. The perpetrator was apparently unaware of the existence of all the systems that ultimately led to his identification. This ignorance is widespread: most citizens do not fully understand the many ways their activities can be monitored and analysed. This knowledge gap benefits surveillance systems, as uninformed people do not know how to protect themselves from surveillance.
It should also be noted that the Kiuru case represents only the tip of the iceberg in terms of technical capabilities. Only those cases in which authorities choose to disclose their use of these systems enter the public domain. It is entirely possible that the same techniques are used in numerous other cases that are never publicly reported. This invisible nature of surveillance is one of its most powerful features.
The perspective of the age of discernment
From the perspective of the age of discernment, the Kiuru case reminds us of the double-edged nature of technology. The same technology that can advance justice by identifying criminals can also enable political control and oppress dissidents. The central challenge of discernment is recognising when technology shifts from serving to controlling, and responding to this shift wisely and courageously.
"A righteous man regardeth the life of his beast: but the tender mercies of the wicked are cruel" (Prov. 12:10, KJV). This verse reminds us that a just society cares for all its members, not only those in power. The use of surveillance technology should be just, transparent, and equitable — not discriminatory or arbitrary.
The Krista Kiuru case ultimately demonstrates that surveillance capacity is no longer a theoretical possibility but a functioning reality. The question is no longer whether authorities are capable of extensive surveillance, but when, upon whom, and with what limitations this surveillance is applied. These questions are fundamentally political and moral, not technical.
12. THE TECHNICAL CAPABILITIES OF FINLAND'S SURVEILLANCE SYSTEMS
The technical capabilities of Finland's surveillance systems significantly exceed what is generally discussed in public debate. The true capacity of these systems becomes comprehensible only when their technical features are examined in detail, and particularly when we consider how different systems work together to create a comprehensive surveillance network. This network enables surveillance that is both broader and deeper than most citizens realise.
Facial recognition and biometric surveillance
Facial recognition and biometric surveillance represent the frontier of surveillance technology in Finland. The technical capabilities of the multi-biometric identification system significantly surpass those of earlier systems. Where earlier systems focused primarily on fingerprints, the new system combines multiple biometric identifiers to create a more multi-dimensional identification profile for each individual.
The algorithmic foundation of the multi-biometric system is based on deep neural networks capable of identifying people far more accurately and versatilely than earlier systems. The system recognises faces even in unfavourable conditions: in poor lighting, partially concealed, or from unusual angles. It can also compare facial images over time and account for age-related changes, making identification even more effective.
The technical accuracy of facial recognition algorithms has improved significantly in recent years. Modern systems achieve over 99.5% identification accuracy in controlled conditions and over 90% accuracy in field conditions. This accuracy makes automatic facial recognition a practically functional surveillance tool that can be implemented on a large scale in public spaces.
The facial recognition system of Finland's P-STUVE project utilises Open-Space Facial Recognition technology, which is capable of identifying individuals from a crowd in motion. The technology is based on a two-stage algorithm: first, face detection from video feeds, and then comparison of detected faces against images in a database. The system is capable of processing multiple video feeds simultaneously, enabling an entire city's camera network to be connected to a single analysis system.
Biometric identification is not limited to faces. Advanced systems also utilise gait recognition, voice recognition, and iris recognition. Gait recognition is particularly significant because it works from a distance and does not require the subject's cooperation or even awareness of the identification. Every person has a unique gait, on the basis of which advanced algorithms can identify a person from up to 50 metres away.
Communications monitoring and analysis
Communications monitoring and analysis form the second major technical capability. Finland's civilian and military intelligence laws enable communications intelligence, which is technically implemented through "splitter" devices installed at network nodes. These devices copy all or part of network traffic for analysis without the user noticing anything unusual.
The screening of communications traffic from vast data streams is performed by special algorithms that identify interesting patterns. These may be keywords, certain communication patterns, unusual connections, or anomalies in traffic that deviates from normal. Finland likely uses XKeyscore-type systems capable of efficiently indexing and analysing vast volumes of network traffic.
A particularly significant technical capability is the ability to break or circumvent encryption technologies. Although strong end-to-end encryption systems such as Signal or WhatsApp are difficult to break at the message level, authorities have other means of accessing encrypted communications. These include:
- Endpoint attacks, where messages are read before encryption or after decryption
- Metadata analysis (who communicates with whom, when, and how much)
- Exploitation of vulnerabilities in communications software
Wiretapping has advanced significantly beyond traditional phone tapping. Current systems are capable of automatic speech recognition and analysis, where an algorithm converts speech to text and analyses its content to identify keywords and topics. The systems also identify speakers by voice and can detect signs of stress in speech, enabling emotional analysis.
Movement and payment surveillance
Movement and payment surveillance form the third major technical capability. The tracking of mobile phone locations is technically sophisticated and based on several overlapping methods:
- Traditional base station tracking locates the phone with accuracy of several hundred metres in urban areas
- WiFi network and Bluetooth device detection refines the location to within tens of metres
- GPS tracking enables accuracy of a few metres outdoors
Operators continuously store data about phone locations as part of normal network operations, and this data is available to authorities under the intelligence laws. Such passive tracking enables the reconstruction of an individual's movements after the fact, which is particularly valuable in investigations.
Public transport travel card data combined with camera surveillance enables the tracking of individuals' movements in cities. Modern systems combine travel ticket data (when and where a card was used) with data produced by facial recognition, creating a complete picture of a person's movements in public transport. This data can be combined with other sources, such as city surveillance cameras, creating a comprehensive picture of a person's movements in the urban environment.
Payment system surveillance is technically particularly advanced. Every digital payment is recorded and traceable. Anti-money laundering (AML) algorithms used by banks continuously monitor all payments and automatically identify unusual patterns, large or suspicious transactions, and deviations from normal payment behaviour. These systems create, in practice, a financial profile of every user of banking services.
Linking online and physical identities
The linking of online and physical identities is the fourth major technical capability. Modern surveillance systems are capable of connecting a person's digital activity with their physical world activities. This occurs through several techniques:
-
"Device fingerprinting" tracks individual devices through browser settings, installed programmes, screen resolution, and other parameters. This enables the identification of a person online even when using different user accounts or changing IP addresses.
-
"Cross-device tracking" identifies when the same person uses different devices (computer, phone, tablet) and combines the data collected from these. This occurs either through login data, behavioural patterns, or the identification of devices on the same network.
-
"Social media intelligence" (SOCMINT) combines data collected from social media accounts with other data sources. Authorities use advanced tools that collect and analyse public social media posts, identify individuals in images, analyse networks, and map opinions.
A particularly effective technique is "identity resolution," in which data collected from different sources is combined and confirmed as belonging to the same individual. This occurs by comparing different identities through multiple data points (name, email, phone number, date of birth, address) and identifying similarities that confirm that the same person is involved.
Integration of technical systems
The integration of technical systems into a unified whole forms the fifth and perhaps most significant technical capability. Finnish authorities are developing integrated information systems that enable the sharing and combining of data between different systems. This integration occurs at both the technical and organisational levels.
At the technical level, integration is implemented through APIs and data warehouses that enable different systems to communicate and exchange data. Modern systems use standardised data formats and identification systems that facilitate the combining of data from different sources.
At the organisational level, authorities are developing shared operating models that enable more effective cooperation and data exchange. This includes joint training, operational protocols, and data exchange channels that enhance the interoperability of systems.
Technological capability often exceeds the limits set by legislation. Although the law restricts the purposes for which data may be used, technically the systems are capable of utilising data far more broadly than is publicly disclosed. This discrepancy between technical capability and legal restrictions is one of the central features of surveillance systems.
"I the LORD search the heart, I try the reins, even to give every man according to his ways, and according to the fruit of his doings" (Jer. 17:10, KJV). This verse reminds us that only God has the true right to see into a person's innermost being. Surveillance systems that seek to map an individual's entire life and personality occupy a spiritually problematic position.
The use of AI in surveillance
A particularly significant technical capability relates to the use of artificial intelligence in surveillance. Finnish authorities use advanced machine learning algorithms capable of identifying patterns in vast volumes of data. These systems learn continuously and improve their accuracy over time.
Predictive analytics is one application of AI. It is based on the analysis of historical data, on the basis of which future behaviour is predicted. Authorities use these models to create risk assessments and target resources at "high-risk" areas or individuals. Such anticipatory action fundamentally changes the nature of authority operations from reactive to proactive.
Behavioural analytics is another AI application in which the algorithm identifies "abnormal" behaviour. The system learns what is normal in a given context and highlights deviations. Such analysis is used, for example, in public spaces, transport, online services, and financial transactions.
The cumulative impact of surveillance capacity
The cumulative impact of these technical capabilities is a system capable of continuous, comprehensive, and automatic surveillance. This system can:
- Identify individuals automatically in public spaces
- Track movements both in real time and historically
- Analyse communications and social contacts
- Map economic activity and spending habits
- Link online and physical world identities
- Make predictions about future behaviour
These technical capabilities significantly exceed what is generally recognised or publicly discussed. Surveillance capacity that was previously depicted only in science fiction is now technically possible and increasingly implemented.
Finland's technological infrastructure
Finland stands out from other countries in the sophistication of its technical infrastructure. Finland has an extensive fibre-optic network, comprehensive mobile network, high digital service usage rates, and strong technological expertise. Together, these factors create an environment in which the deployment of surveillance technologies is technically easier than in many other countries.
The technical expertise of Finnish authorities is also of a high calibre. Finland has invested significantly in cybersecurity and digital capabilities, which is also reflected in surveillance capacity. Finland's intelligence services and law enforcement authorities work closely with technology companies and utilise the latest technologies.
The invisibility of surveillance
A central feature of a modern surveillance system is its invisibility. Unlike traditional surveillance methods, which were often visible and concrete (such as physical observers or clearly distinguishable surveillance cameras), current systems operate largely out of sight. This invisibility makes the systems more effective but also more problematic from the standpoint of democracy and transparency.
Data-driven surveillance takes place at the level of bits and algorithmic analysis, without a visible physical presence. Surveillance is embedded in everyday systems and infrastructure in a way that makes it imperceptible. This invisibility leads to a situation where surveillance becomes normalised and part of everyday life without being questioned.
The perspective of the age of discernment
From the perspective of the age of discernment, the development of technical capabilities calls us to moral and spiritual assessment. Technology itself is neither good nor evil, but its purposes and effects on society and individuals require critical examination. Key questions include:
Who has the right to see into a person's "innermost being" — their movements, their relationships, their thoughts, and their feelings? Traditionally, this right has belonged only to God, but modern surveillance systems seek to imitate this omniscience.
How does surveillance affect a person's inner freedom and development? Constant observation can lead to self-censorship and internalised surveillance, where a person moulds their behaviour and even their thoughts to conform to external expectations.
What is the right balance between security and freedom? Surveillance is often justified by security, but true security is founded on trust and community, not on control.
"But all things that are reproved are made manifest by the light: for whatsoever doth make manifest is light" (Eph. 5:13, KJV). This verse reminds us that in the light of truth, even invisible structures become visible. The age of discernment calls us to bring the true capabilities and effects of surveillance systems to light, so that they can be assessed honestly and comprehensively.
The speed of technological development often exceeds society's ability to adapt to and regulate new technologies. This "technological determinism" leads to a situation where technology determines the development of society rather than the other way around. In the age of discernment, we must ask what kind of technological future we want and how we can ensure that technology serves humanity rather than ruling it.
Making conscious and moral choices in the age of surveillance technology requires an understanding of the true capabilities and effects of these systems. This understanding is possible only if the systems are discussed openly and honestly, without secrecy or misleading rhetoric. The truth about technology is the first step toward a wiser and more humane technological future.
13. THE PROPHECIES OF REVELATION AND THE DEVELOPMENT OF SURVEILLANCE TECHNOLOGY
The parallels between the prophecies of the Book of Revelation and the development of modern surveillance technology are significant and deserve serious examination. While caution is warranted in interpretation, the development of technology has led to a situation where many prophecies previously considered only symbolic have found concrete technological counterparts. This convergence calls for a deeper understanding of the spiritual significance of these prophecies in the age of discernment.
The prophecy of the mark and its interpretation
Revelation 13:16–17 contains one of the most significant prophecies related to control systems: "And he causeth all, both small and great, rich and poor, free and bond, to receive a mark in their right hand, or in their foreheads: And that no man might buy or sell, save he that had the mark, or the name of the beast, or the number of his name" (KJV). This description of a global control system has provoked discussion for centuries, but only modern technology has made its literal fulfilment possible.
Traditionally, the mark has been interpreted as a literal physical mark, such as the tattooed numbers used in Nazi concentration camps on the left forearm. Modern technology, however, has made physical marking unnecessary. A digital identity serves as a "mark" that is simultaneously invisible yet omnipresent. This digital mark is paradoxically both more immaterial and more concrete than a physical mark could ever be, as it follows the individual everywhere and determines their opportunities to participate in society.
Biometric identification in the light of prophecy
Biometric identification brings a new dimension to the interpretation of the prophecy. Revelation's description of a mark "in their right hand, or in their foreheads" finds a literal counterpart in biometric identification systems that use precisely hands (fingerprints, palm vein scanning) and faces (facial recognition, iris recognition) to identify people. These body parts now serve as concrete "identifiers" that determine access to systems and services.
The development of subdermal microchips has taken this to an even more concrete level. In Sweden, for example, thousands of people have voluntarily had RFID chips implanted in their hands for access control, payments, and authentication. These chips function literally as a "mark in the right hand," enabling door opening, payment, or system login with a simple hand movement. Although these implants are currently voluntary, they create an infrastructure that could become mandatory in the future.
Digital identity and a global identification system
Digital identity brings us closer to the possibility of a global identification system. The EU's digital identity wallet (EUDI) and similar initiatives aim to create standardised digital identities that enable authentication across all services. The goal of these systems is to create "one identity for all services," which corresponds to the prophecy's description of a universal mark.
In the case of digital identity, the "mark" is not physical but a digital reality — a totality of data points representing the individual online and in the real world. This data-constituted identity is paradoxically both more abstract and more concrete than a physical mark. It is more abstract because it cannot be seen or touched, but more concrete because it determines an individual's possibilities and rights in ways that a physical mark could never achieve.
Mechanisms of economic control
Particularly significant is the prophecy's reference to economic control: "no man might buy or sell, save he that had the mark." This economic dimension is central to the development of modern surveillance technology. Central bank digital currencies (CBDC) are creating an infrastructure that enables significant economic control.
The digital euro, the digital yuan, and other CBDCs enable the real-time monitoring and control of every transaction. The "programmability" of these currencies means that money can be restricted: it can be used only for certain purposes, in certain places, or at certain times. An individual's economic activity can also be blocked entirely if they are "marked" as untrustworthy in the system.
The disappearance of cash reinforces this control further. Cash is the last anonymous and fully free payment method that does not require third-party approval. When cash disappears, all economic activity becomes visible and controllable. This transition literally creates a situation where "no man might buy or sell" without the system's approval.
Social credit scoring and behavioural steering
Social credit scoring, which is most advanced in China, creates a system in which a person's rights are determined by their "trustworthiness." This trustworthiness is measured algorithmically on the basis of data collected from every aspect of the person's activity. A low score can lead to restrictions on travel, housing, education, and economic activity — literally preventing a person from "buying or selling" normally.
It is noteworthy that according to the prophecy, the mark may be "the name of the beast, or the number of his name." This refers to a system in which the individual is identified by a code or number. In today's systems, this is fulfilled literally: we are represented digitally by personal identity codes, customer numbers, user IDs, and passwords. These digital identifiers are essential for participation in society, just as the prophecy describes.
Identification and marking technologies
"The number of the beast, 666" (Rev. 13:18) has traditionally prompted many interpretations. One interesting technological connection is found in the barcode system, whose basic identifiers use three longer bars at the beginning, middle, and end. These bars encode as the number 6, creating the structure 6-6-6. Although this is just one possible interpretation, it demonstrates how the symbols of the prophecy can find technological counterparts.
RFID technology and other wireless identification systems provide another concrete point of comparison with the prophecy. These technologies enable remote identification and tracking without physical contact or even line of sight. They function as an invisible "mark" that nonetheless determines access to services and spaces.
A more nuanced interpretation of the mark relates to internalised control. Revelation's description of the mark "in the forehead" can be symbolically interpreted as referring to thought and identity. Modern surveillance systems profoundly influence how people think and how they see themselves. They create a state of internalised surveillance in which external control becomes internal self-censorship.
"Forasmuch as ye are manifestly declared to be the epistle of Christ ministered by us, written not with ink, but with the Spirit of the living God; not in tables of stone, but in fleshy tables of the heart" (2 Cor. 3:3, KJV). This verse reminds Christians that their true identity and "marking" comes from God, not from any earthly system. This spiritual reality stands in opposition to the worldly identification system.
Crisis-enabled rapid deployment of systems
The digital health passes developed during the pandemic provide a concrete example of how quickly a global identification system can be deployed. Health passes were implemented within months and restricted access to public spaces, restaurants, shops, and travel. Although these systems were later withdrawn, they demonstrated how rapidly a global control system can be implemented and normalised.
The prophecies of Revelation also reflect a broader dynamic of surveillance. Revelation describes a world order in which state and religion work together to create a global control system. This description resembles current systems in which the state, large corporations, and ideological movements collaborate to create a unified surveillance and control system.
Although smart devices and digital identities were not created with "evil" intent, they create an infrastructure that enables significant control. This infrastructure can change its character in crisis situations, when societal norms and restrictions shift. These technologies are not in themselves manifestations of "evil," but they create a new kind of vulnerability that can be exploited for control.
Soft coercion and persuasion as means of control
The fulfilment of the prophecy does not necessarily require overt compulsion. A modern control system relies more on persuasion, convenience, and social pressure than on coercion. People adopt surveillance technologies voluntarily because they offer convenience, security, and social acceptance. This "soft totalitarianism" is more effective than coercive control because it meets less resistance.
"Beloved, believe not every spirit, but try the spirits whether they are of God: because many false prophets are gone out into the world" (1 John 4:1, KJV). This verse reminds us of the importance of critical discernment in the age of technology. We must "try" systems and technologies, evaluate their true effects and underlying values, and not simply accept them uncritically.
The Christian response to the challenges of surveillance technology
The technological fulfilment of Revelation's prophecies raises questions about the Christian response. How should Christians relate to evolving surveillance systems? There is no simple answer to this question, but several principles can guide reflection:
The first principle is that technology itself is neither evil nor good — its purpose and effects determine its moral character. Christians can use technology for good purposes while being aware of its potential dangers.
The second principle is that the primary allegiance of Christians is to God, not to earthly systems. If an earthly system demands actions that conflict with God's law, the Christian's duty is to obey God rather than men (Acts 5:29).
The third principle is the balance between freedom and responsibility. Christians value both their own freedom and their responsibility to the community. This means they can accept reasonable surveillance and restrictions that serve the common good but resist surveillance that threatens fundamental freedoms and human dignity.
The challenges and opportunities of the age of discernment
The central challenge of the age of discernment is to recognise when technology shifts from serving humanity to controlling it. This distinction is not always clear, and it requires both spiritual and technical understanding. Christians are called to be "wise as serpents, and harmless as doves" (Matt. 10:16, KJV) in the age of technology.
"And be not conformed to this world: but be ye transformed by the renewing of your mind, that ye may prove what is that good, and acceptable, and perfect, will of God" (Rom. 12:2, KJV). This verse reminds us that we should not uncritically accept prevailing systems but evaluate them in the light of God's will. This evaluation requires continuous renewal of the mind and spiritual discernment.
The prophecies of Revelation call us to vigilance, but not to fear or despair. Christians have always had a hope that transcends earthly power and control. This hope is founded on the faith that God is ultimately the Lord of history and that no earthly power can separate believers from the love of God (Rom. 8:38–39).
Spiritual preparation in the age of technology
Preparation for the age of discernment does not primarily mean avoiding technology but developing spiritual vigilance and discernment. It means knowing the truth that sets free (John 8:32) and living in the presence of God in a world that increasingly seeks to replace God's role with technological surveillance and control.
"And they overcame him by the blood of the Lamb, and by the word of their testimony; and they loved not their lives unto the death" (Rev. 12:11, KJV). This verse reminds us that ultimate victory is founded on faith and the speaking of truth, not on technological solutions or earthly power.
The prophecies of Revelation offer us a map for understanding temporal events in a spiritual context. They do not call us to technocentrism, in which all technology is seen as evil, but to spiritual discernment, in which we recognise the true nature and effects of technology.
Identity and loyalty in the world of technology
The mark and its resistance are not primarily technological questions but questions of inner loyalty and identity. The true mark, as Revelation describes it, ultimately relates to a deep commitment to a particular value system and identity. Technology can express this commitment but does not define it.
In the age of discernment, Christians are called to be "in the world, but not of the world" (John 17:14–16). This means that they use technology to serve God and their neighbours but do not allow technology to define their identity or their loyalty. Their ultimate identity is in Christ, not in digital systems.
Ultimately, the connection between the prophecies of Revelation and modern technology reminds us of the temporariness of earthly systems and the permanence of the Kingdom of God. We need not fear technology or control systems, but we must remain vigilant and faithful to truth that transcends all earthly power systems.
"I know thy works: behold, I have set before thee an open door, and no man can shut it: for thou hast a little strength, and hast kept my word, and hast not denied my name" (Rev. 3:8, KJV). This verse reminds us that external power and control cannot rob the inner freedom of those who remain faithful to truth. In the age of discernment, this inner freedom is more precious than ever.
14. IN CLOSING: THE AGE OF DISCERNMENT IN THE FACE OF SURVEILLANCE TECHNOLOGY
The historical continuum of surveillance technology has travelled a long road from IBM's punch card systems to today's digital surveillance systems. Understanding this continuum is essential for facing the challenges of our time. Surveillance systems do not emerge in a vacuum but develop gradually, building upon the foundation laid by earlier technology. It is precisely by recognising this continuum that we can see the direction of the future and prepare for the challenges of the age of discernment.
The incremental construction of surveillance systems
The construction of a surveillance system occurs in small, imperceptible steps. Nazi Germany's surveillance apparatus did not emerge overnight but developed in stages, beginning with seemingly innocent censuses and progressing incrementally toward ever more invasive surveillance and control. This incremental progression is repeated in the development of modern surveillance systems. Each individual step is presented as limited and justified, but together they form a whole that significantly alters the relationship between citizen and state.
Incremental progression is particularly dangerous because it leads to the normalisation of surveillance. As each new form of surveillance is introduced in response to a specific need or threat, it is more easily accepted. Gradually, surveillance methods previously considered unthinkable become everyday, unquestioned elements of society's structure. Like the frog in slowly heating water, society adapts to the increase in surveillance without noticing how significantly freedom and privacy have been eroded.
The balance between security and freedom
The tension between security and freedom is a central challenge of the age of discernment. Surveillance systems are always justified by security, and most people have a natural tendency to prioritise security at the expense of freedom. This tendency intensifies in crisis situations, when fear overrides concerns about privacy and freedom. The lesson of history, however, is clear: freedom once lost is difficult to reclaim, and surveillance powers granted in crisis generally remain in force after the crisis has passed.
"Stand fast therefore in the liberty wherewith Christ hath made us free, and be not entangled again with the yoke of bondage" (Gal. 5:1, KJV). This verse reminds us of the value of freedom and of the dangers that threaten it. In the age of surveillance technology, freedom is not only physical but also digital, mental, and spiritual. This freedom requires active defence and conscious choices in a world that increasingly encourages surrendering freedom for the sake of security or convenience.
The responsibility of speaking truth
The Christian's responsibility to speak truth is particularly important in the age of surveillance systems. The narratives of authorities, corporations, and media about surveillance technology often emphasise its benefits and downplay its risks. Christians have a responsibility to speak truth to power, to question official narratives, and to bring to light less-discussed dimensions. This truth-speaking is not merely technical but also spiritual: it reveals the values and principles underlying these systems.
"And ye shall know the truth, and the truth shall make you free" (John 8:32, KJV). This verse underscores the deep connection between truth and freedom. Surveillance systems are often based on deception and secrecy: they collect information about people while concealing their own operations. Revealing the truth about these systems is the first step toward freedom from their power.
Learning from the warnings of history
The warnings of history are clear, but heeding them requires humility and attentiveness. Germans of the 1930s did not believe that their society could slide into totalitarianism, just as many Westerners today do not believe that their democratic societies could develop into surveillance states. Yet history demonstrates that no society is immune to this development, particularly in times of crisis, when fundamental rights are more readily relinquished.
The danger of gradual adaptation is particularly great in today's digital environment. Younger generations are growing up in a world where constant surveillance has been normalised as part of life. They have never experienced a time before large-scale digital surveillance, so they have no frame of reference for evaluating the current situation. This generational gap in experience makes the resistance to surveillance even more difficult.
The moral dimension of technology
The relationship between technology and morality is a central question of the age of discernment. Technology itself is neither good nor bad, but neither is it neutral. Technology develops under the guidance of certain values, goals, and power structures. It reflects the moral choices of its developers and users and influences the thinking and behaviour of its users. The age of discernment calls us to recognise these values and effects and to make conscious choices about what technology is developed and used.
"All things are lawful unto me, but all things are not expedient: all things are lawful for me, but I will not be brought under the power of any" (1 Cor. 6:12, KJV). This verse offers a wise principle for the use of technology. The freedom to use technology includes the condition that we must not allow it to rule over us. This requires conscious reflection on how technology affects us and a willingness to limit its use when it threatens freedom or values.
The spiritual dimension of exposing surveillance
Exposing surveillance systems is not merely a technical or political task but a profoundly spiritual calling. It requires the courage to face truth even when it is uncomfortable, and to challenge power structures that benefit from surveillance. This calling is not limited to researchers or activists but extends to every Christian committed to truth and freedom.
"What? know ye not that your body is the temple of the Holy Ghost which is in you, which ye have of God, and ye are not your own?" (1 Cor. 6:19, KJV). This verse reminds us that our bodies and identities ultimately belong to God, not to earthly systems. Surveillance systems seek to take possession of precisely these dimensions of identity and body, turning people into data points in algorithmic control. The Christian response is to affirm our identity as children of God, not as products of systems.
The revealing of priorities and commitments
The age of discernment reveals the deepest priorities and commitments. It challenges us to ask what we truly value: comfort or freedom, the feeling of security or true security in God, social acceptance or faithfulness to truth. These choices are not theoretical but concrete and daily, particularly in a world permeated by digital technology.
Conscious choices in the face of surveillance technology require both understanding and courage. Understanding begins with an awareness of history: how surveillance systems have developed and what consequences they have had. It continues with mapping the current situation: what systems are in use, how they function, and what effects they have. This understanding enables conscious choices about our own participation in these systems.
Challenging technological determinism
Resisting technological determinism is part of the challenge of the age of discernment. Technological determinism is a way of thinking that holds that the development of technology is inevitable and society must adapt to it. This way of thinking takes power from people and gives it to technological systems and their developers. The Christian response is to emphasise human agency: the power and responsibility to make choices regarding technology, to determine the direction of its development, and to set limits on it.
"I will go before thee, and make the crooked places straight: I will break in pieces the gates of brass, and cut in sunder the bars of iron" (Isa. 45:2, KJV). This verse reminds us that God goes before us in the challenges of the age of discernment. No system, however advanced or pervasive, can separate us from God's care and guidance. This assurance gives us the courage to face the threats and challenges of surveillance systems.
Defending human dignity in a technological environment
Defending human dignity is central to responding to the technical coldness of surveillance systems. Technological systems have a tendency to reduce people to data points, identification numbers, and algorithmic objects. This reductionism loses sight of a person's uniqueness, dignity, and inalienable value as the image of God. The Christian response is to affirm human dignity in all contexts and resist systems that seek to undermine it.
Strengthening community serves as a counterweight to the isolating effects of surveillance systems. Surveillance creates distrust and fear, which weakens community and mutual trust between people. Strong communities, particularly faith communities, can serve as a counterforce to this development. They offer a space in which a person is seen and accepted as a whole person, not merely as a surveillance subject or a risk assessment.
"Now the Lord is that Spirit: and where the Spirit of the Lord is, there is liberty" (2 Cor. 3:17, KJV). This verse reminds us that ultimate freedom does not depend on external circumstances but on spiritual reality. Even as external surveillance increases, in the presence of God there is always a space of freedom that no earthly system can control. This freedom is not an escape from reality but a deeper encounter with reality from God's perspective.
Future technologies and moral principles
The development of technology has not stopped, and new innovations bring both opportunities and challenges. Artificial intelligence, quantum computers, biotechnology, and neural interface systems will change the nature of surveillance in ways not yet fully understood. The development of these technologies does not, however, change the central moral and spiritual questions concerning human dignity, freedom, and truth. These principles remain our compass in the midst of technological change.
The truth behind surveillance technology is that it embodies the age-old human drive to dominate and control. This drive did not begin in the digital age but has been present throughout history. Modern surveillance technologies are merely the latest manifestation of this ancient wound in the heart of humanity. Recognising this truth helps us see technology as part of a broader spiritual struggle, not merely as a technical problem.
The balance between critical awareness and hope
The age of discernment calls for balance. We must avoid becoming captives of technological determinism or cultural pessimism, but we must also not be naive about the dangers of technology. Balance is found in critical awareness that recognises both the possibilities and threats of technology and makes conscious choices on the basis of this understanding.
"But he that shall endure unto the end, the same shall be saved" (Matt. 24:13, KJV). This verse reminds us of the importance of endurance in a long struggle. The development of surveillance systems is a continuous process requiring ongoing vigilance and action. Every generation faces new challenges and opportunities, and each is called to defend freedom and truth in its own context.
At the heart of the age of discernment lies not technology but spiritual reality. Surveillance technologies are not merely technical systems but embody a deeper struggle over power, identity, and truth. In this struggle, truth is the most powerful weapon and freedom the most precious treasure. In facing the challenges of surveillance systems, awareness that we live as part of a greater story in which truth and freedom ultimately prevail is essential.
"But I will hope continually, and will yet praise thee more and more" (Ps. 71:14, KJV). This verse expresses the fundamental attitude of the Christian even in facing the challenges of surveillance technology: hope and praise. Hope means trust that God is at work and that truth will come to light. Praise means that surveillance systems are not allowed to define reality, but that we live in the presence of God, which transcends all earthly power systems.
Personal choices and responsibility
Ultimately, each person is called to make choices in the age of discernment. These choices are not only external but also internal: what information we share, what technologies we use, how we relate to surveillance, how we understand identity in the digital world. These choices determine what kind of future we build for ourselves and for coming generations.
Surveillance systems are effective but not all-powerful. Their power is partly based on an illusion in which they appear inevitable and irresistible. Exposing this illusion is the first step toward a freer future. The truth about surveillance systems — their operations, limitations, and effects — liberates us from their mental hold, even though they may continue to operate in the physical world.
The history of humanity is full of examples of those who have remained faithful to truth in the face of power systems. Their example reminds us that the choices of individuals matter, and that every act of honesty and courage influences history in ways that cannot always be foreseen. These examples inspire us to make our own choices in the age of discernment.
"For God hath not given us the spirit of fear; but of power, and of love, and of a sound mind" (2 Tim. 1:7, KJV). This verse reminds us that God has equipped us to face the challenges of our time. Power gives the courage to act, love guides us to act for the good of others, and a sound mind helps us navigate through complex questions.
The privilege of living in the age of discernment
Living in the age of discernment is not merely a challenge but also a privilege. It is part of a historical continuum in which defenders of truth have always risen to resist the abuse of power. Our time demands technical understanding combined with spiritual wisdom — the ability to see through digital systems to the spiritual truths that lie behind them.
Understanding the arc of surveillance technology from IBM's punch cards to modern digital systems reminds us that technology does not develop in a vacuum. It carries with it the ballast of its history and moral choices. This understanding calls us to make conscious choices in the development, use, and regulation of technology — choices that respect human dignity, protect freedom, and serve truth.
Truth as a liberating force
The truth shall make us free. This principle applies equally in the age of surveillance technology. Truth about surveillance systems — their history, development, and effects — liberates us from their power. It provides the opportunity to make conscious choices rather than being passive objects of development. This truth is not merely technical but also moral and spiritual: it touches the deepest questions about humanity, freedom, and where our ultimate loyalty belongs.
"For my people have committed two evils; they have forsaken me the fountain of living waters, and hewed them out cisterns, broken cisterns, that can hold no water" (Jer. 2:13, KJV). This verse aptly describes the paradox of technological surveillance: in seeking security and certainty through surveillance, we often abandon the deeper security found in trust, community, and the presence of God. Surveillance systems are like broken cisterns that promise safety but cannot truly deliver it.
The age of discernment calls each person to personal responsibility. Moral choices cannot be outsourced to systems, institutions, or technology. Each person is responsible for how they relate to surveillance, what technologies they use, and what values they defend. This responsibility is both a burden and a privilege: it is part of the calling to be witnesses of truth in a world that increasingly relies on illusions and falsehoods.
Final words
"Having done all, let us stand firm." The development of surveillance technology from IBM's punch cards to the digital surveillance society has been a long and complex journey. It has revealed both the potential and the dangers of technology. The age of discernment calls us today to see this development clearly, to evaluate it wisely, and to act courageously for truth and freedom. This call is not merely part of a historical struggle but part of an eternal striving toward a world where technology serves humanity rather than ruling it.